by Josef Weiss
December 4, 2023
Understanding Cyber Exposure requires that the data collected by Tenable Vulnerability Management is trusted and verifiable. Tenable Vulnerability Management provides several plugins that assist in determining scan status and provides a level of trust for risk managers. This report brings together all the plugins used to verify successful authentication of assets during vulnerability scans, providing security administrators visibility into areas of concern so that the appropriate actions can be taken.
Authentication is a process of connecting to a system by providing credentials to gain access. Tenable Vulnerability Management scans systems by using different network protocols (SSH, SMB, HTTPS, SNMP, etc.) to gain access to the target asset. For example, logging into a remote host via SSH using a username and password is a method of authentication. Each asset can allow authentication using several protocols. Assets with more than one available authentication protocol, for example a Windows server running a SQL server, could report both authentication success and failure. Understanding this fact during analysis is key to determining if the system was successfully scanned or not. While in many cases the successful authentication of an asset may seem binary, there are many examples of successfully scanned systems with authentication failures. Tenable recommends that system administrators review all of the failures and investigate the services which are enabled on the asset for a complete analysis.
Local checks are a feature in Tenable Vulnerability Management scans, which enable the scanner to perform security checks on the target asset. Some general checks function without full administrator credentials, but when all possible general checks are completed, Tenable Vulnerability Management verifies privilege escalation to perform more accurate local checks. The local checks always require authentication and often require elevated privileges. Local checks for major operating systems with security advisories numbering in the thousands are often grouped into their own plugin family, but local check plugins also exist in other families such as Firewalls or Misc.
Local checks require authentication and occur after successful authentication has been established. The following criteria must be satisfied to utilize local checks:
- The target device or operating system must be identifiable by Tenable Vulnerability Management
- Local check plugins must be available for the identified device or operating system
- The information needed to enable local checks for the particular device or operating system must be obtainable from the target asset
- Except in particular circumstances, such as scanning localhost, remote authentication must first be successful before local checks are enabled
Local checks are required to ensure that scans are complete and accurate. Users enable local checks by providing credentials with elevated privileges, or administrative access, or by deploying Nessus Agents. Tenable Vulnerability Management requires privileged access to provide a comprehensive assessment of risk on an asset. The more access to a system Tenable Vulnerability Management has, the more complete the vulnerability detection.
Security leaders need to SEE everything, PREDICT what matters most and ACT to address cyber risk and effectively align cybersecurity initiatives with business objectives. Tenable.io discovers and analyzes assets continuously to provide an accurate and unified view of an organization’s security posture. The requirements for this dashboard are: Tenable.io Vulnerability Management (Nessus, NNM).
Chapters
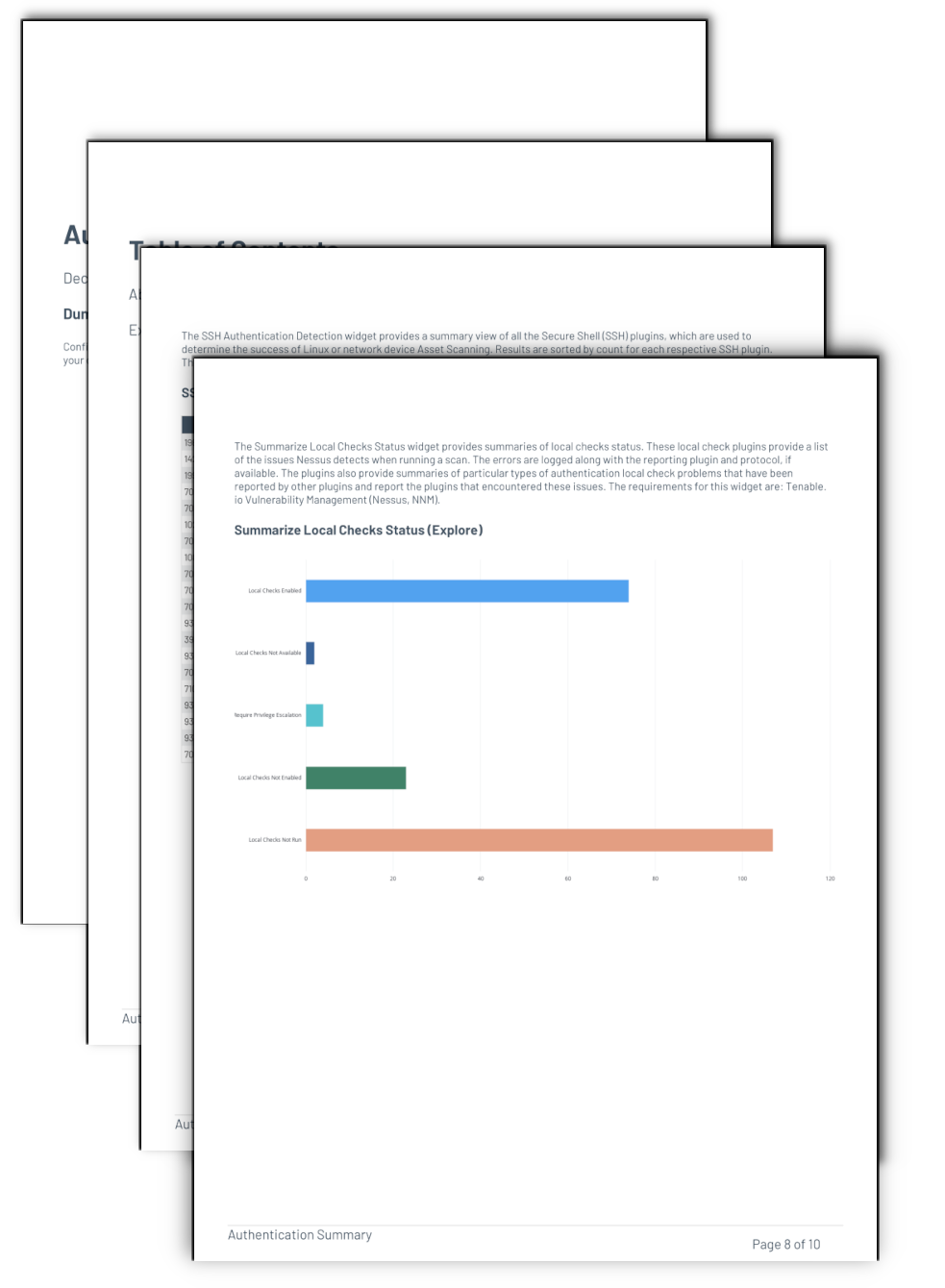
Executive Summary – The chapter contains several elements which provide the organization with a clear and simplified method to track and troubleshoot authentication related problems. By grouping authentication plugins into diagnostic context, the report shows administrators areas of concern to focus on. The SMB Authentication Detection element provides a summary view of all the informational SMB plugins, which are used to determine the success of Windows asset scans. The SSH Authentication Detection element provides a summary view of all the Secure Shell (SSH) plugins, which are used to determine the success of Linux or network device Asset Scanning. The Windows Access Checks element provides an indication of the scan health of Windows systems. The Summarize Local Checks Status element provides summaries of local checks status. The Authentication Searches element provides a series of useful queries to help troubleshoot authentication problems. And the Local Authentication Information element brings focus to the plugins used to authenticate to a remote host, gathers the information necessary for local checks, and enables local checks.