The Verizon Data Breach Investigation Report (DBIR), first published in 2008, is an annual publication that analyzes information security incidents from public and private organizations, with a focus on data breaches. Data breaches continue to have a major financial impact on organizations, as well as an impact on their reputations. Tenable Network Security offers dashboards and Assurance Report Cards (ARCs) that organizations can use to check themselves against the common threats described in the Verizon DBIR. As in previous years, the 2016 DBIR notes that a vast majority of all attacks fall into a few basic patterns. Throughout this and past years’ reports, best practices are noted for each pattern that can assist in thwarting the attacks, and some of the best practices can assist in thwarting multiple attack patterns. The Crimeware and Cyber-Espionage patterns mention the best practice of patching and correctly configuring web browsers, and the Web App Attacks pattern discusses the importance of securing web application.
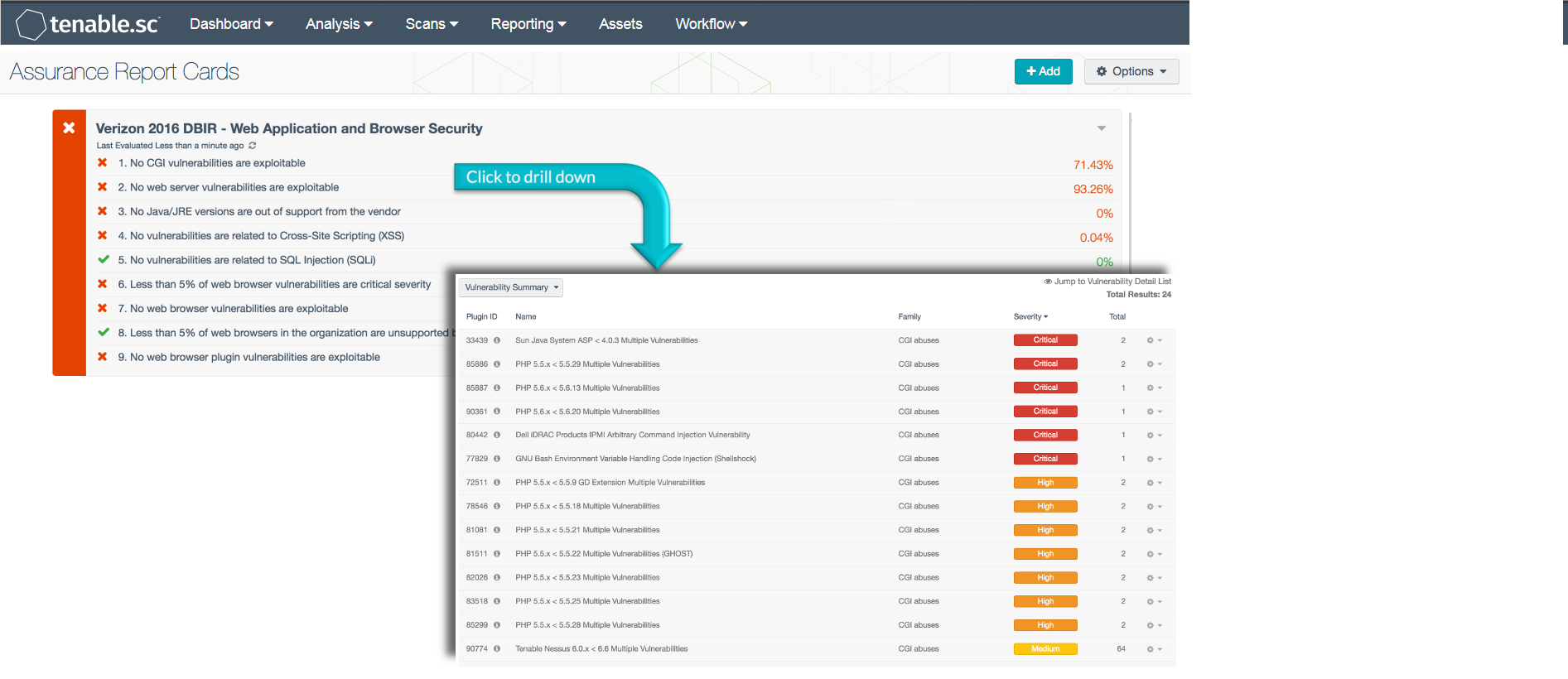
Vulnerable web applications and browsers can pose a great security risk to the network. Since web platforms communicate with the outside world over the Internet, the web applications are often targeted by outside attackers. The use of outdated or vulnerable web browsers may allow the network to be compromised. Based on the best practices described in the Verizon DBIR, the Web Application and Browser Security ARC monitors common web application and browser vulnerabilities, as well as tracks outdated software. This information can assist the organization in reducing the chances of a data breach by updating web browsers, patching web application vulnerabilities, and disabling vulnerable plugins.
This ARC assists organizations in improving their vulnerability remediation efforts. Systems and vulnerabilities are identified using active scans by Nessus. Policy statements are included that report web application vulnerabilities, common web exploits, and unsupported software. Unpatched vulnerabilities, unsupported software, and exploitable vulnerabilities can leave a network exposed to malicious activity. Ensuring that systems are scanned and updated regularly is key to monitoring and remediating the vulnerabilities on systems within a network in order to mitigate risk.
The information provided in this ARC provides a baseline to measure the effectiveness of an organization's risk assessment efforts and identifies whether the policies that are currently being enforced are effective. Policy statements can be customized as needed to meet organizational requirements.
This ARC is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Security Industry Trends.
The dashboard requirements are:
- Tenable.sc 5.3.1
- Nessus 8.5.1
Tenable's Tenable.sc Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. Tenable.sc is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. By integrating with Nessus, Tenable.sc CV’s continuous network monitoring is able to track vulnerabilities and mitigations across the enterprise.
The following policy statements are included in this ARC:
No CGI vulnerabilities are exploitable: This policy statement displays the ratio of exploitable web application vulnerabilities to total web application vulnerabilities. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Web application vulnerabilities can expose systems to additional risk of exploitation. This policy statement will help to monitor and identify vulnerabilities that can increase the risk to an organization. Web application vulnerabilities have a greater attack surface due to their exposure to the Internet. These exploitable vulnerabilities should be remediated quickly to improve security.
No web server vulnerabilities are exploitable: This policy statement displays the ratio of exploitable web server vulnerabilities to total web server vulnerabilities. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Web server vulnerabilities can expose systems to additional risk of exploitation. This policy statement will help to monitor and identify vulnerabilities that can increase the risk to an organization. Web server vulnerabilities have a greater attack surface due to their exposure to the Internet. These exploitable vulnerabilities should be remediated quickly to improve security.
No Java/JRE versions are out of support from the vendor: This policy statement displays the ratio of unsupported Java and JRE versions to total Java and JRE installations. If the policy statement is met, the result is displayed in green; otherwise, the result is displayed in red. Unsupported instances of Java and JRE do not receive updates and are prone to exploitation. This policy statement will help to identify versions of Java and JRE that are out of regular, extended, or premier support. Unsupported installations of Java and JRE should be updated or upgraded to reduce the risk of exploitation.
No web application vulnerabilities are related to Cross-Site Scripting (XSS): This policy statement displays the ratio of Cross-Site Scripting (XSS) vulnerabilities to total vulnerabilities. If the policy statement is met, the result is displayed in green; otherwise, the result is displayed in red. Exploited XSS vulnerabilities can result in further compromise to systems. This policy statement will help to identify and monitor XSS vulnerabilities that could be exploited. XSS vulnerabilities should be remediated to reduce the risk of network compromise.
No web application vulnerabilities are related to SQL Injection (SQLi): This policy statement displays the ratio of SQL Injection (SQLi) vulnerabilities to total vulnerabilities. If the policy statement is met, the result is displayed in green; otherwise, the result is displayed in red. Exploited SQLi vulnerabilities can result in further compromise to systems. This policy statement will help to identify and monitor SQLi vulnerabilities that could be exploited. SQLi vulnerabilities should be remediated to reduce the risk of network compromise.
Less than 5% of web browser vulnerabilities are critical severity: This policy statement displays the ratio of critical web browser vulnerabilities to total web browser vulnerabilities. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Critical web browser vulnerabilities can expose systems to additional risk of exploitation. This policy statement will help to monitor and identify vulnerabilities that can increase the risk to an organization. Web browser vulnerabilities may be susceptible to exploitation, and critical vulnerabilities should be remediated quickly to improve security.
No web browser vulnerabilities are exploitable: This policy statement displays the ratio of exploitable web browser vulnerabilities to total web browser vulnerabilities. If the policy statement is met, the result is displayed in green; otherwise, the result is displayed in red. Exploited web browser vulnerabilities can result in further compromise to systems. This policy statement will help to identify and monitor vulnerabilities that could be exploited. Web browser vulnerabilities that are exploitable should be remediated to reduce the risk of network compromise.
Less than 5% of web browsers in the organization are unsupported by the vendor: This policy statement displays the ratio of unsupported web browsers to total web browsers. If the policy statement is met, the result is displayed in green; otherwise, the result is displayed in red. Unsupported web browsers may be susceptible to exploitation or attack. This policy statement will help to identify web browsers that are unsupported. Web browsers that are unsupported should be updated, upgraded, or uninstalled to reduce the likelihood of exploitation.
No web browser plugin vulnerabilities are exploitable: This policy statement displays the ratio of exploitable web browser plugin vulnerabilities to total web browser plugin vulnerabilities. If the policy statement is met, the result is displayed in green; otherwise, the result is displayed in red. Exploited web browser plugin vulnerabilities can result in further compromise to systems. This policy statement will help to identify and monitor plugin vulnerabilities that could be exploited. Web browser plugin vulnerabilities that are exploitable should be remediated to reduce the risk of network compromise.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success