The Payment Card Industry Security Standards Council (PCI SSC) maintains, evolves, and promotes Payment Card Industry standards for the safety of cardholder data across the globe. The PCI SSC provides technical and operational requirements for organizations accepting or processing payment transactions. The guidance also applies to software developers and manufacturers of applications and devices used in those transactions.
The Payment Card Industry Data Security Standard (PCI DSS) helps entities understand and implement standards for security policies, technologies and ongoing processes that protect their payment systems from breaches and theft of cardholder data. The standards have historically been revised on a 2-3 year cycle, but the PCI SSC is transitioning to a posture of revising the PCI DSS as required based on changes to the current threat landscape. The current standard revision is PCI DSS Version 4.x. Any organization that handles payment card information must comply with the PCI DSS and must demonstrate compliance annually. Tenable Security Center is able to help organizations monitor ongoing PCI DSS compliance.
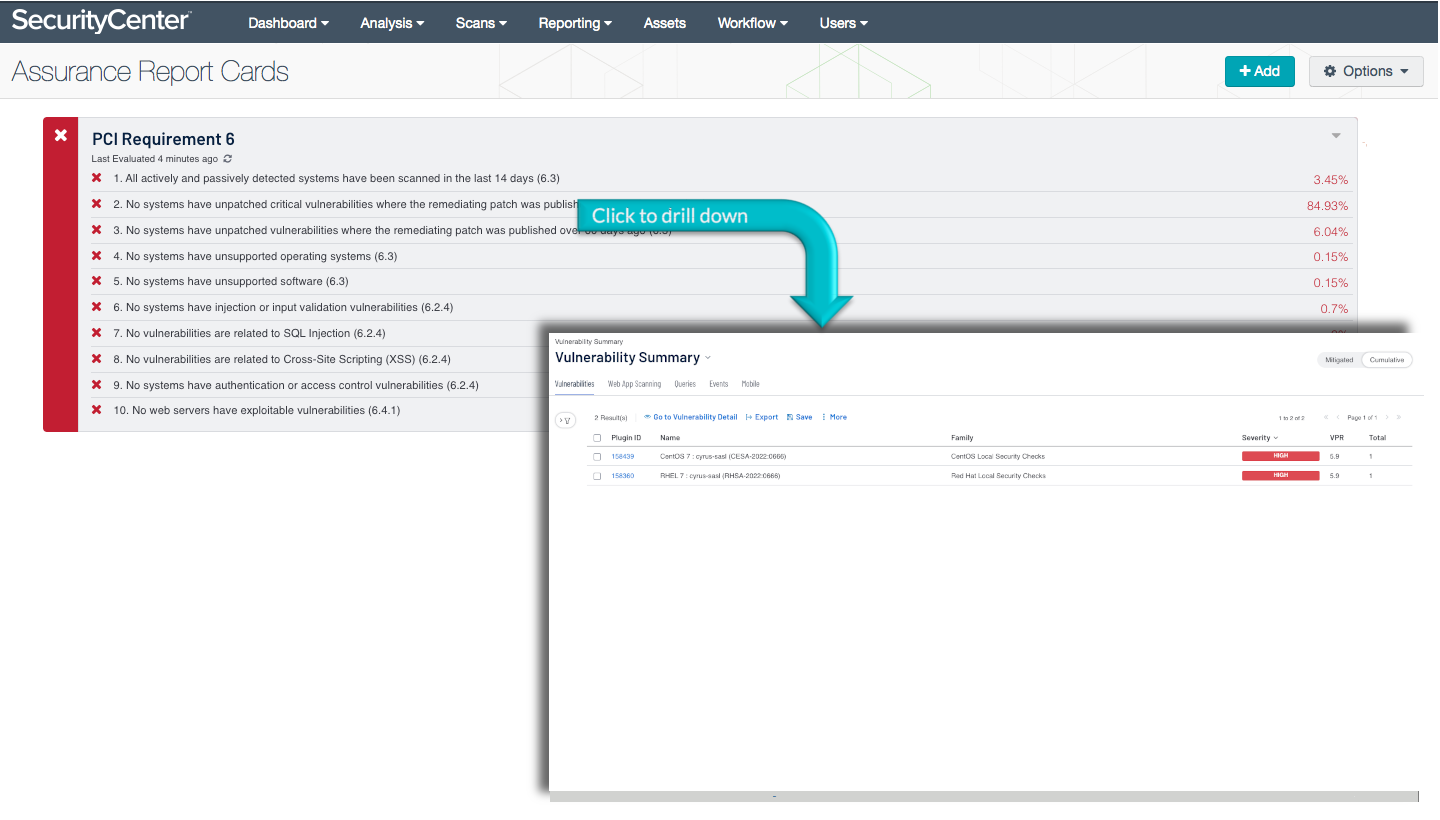
The PCI Requirement 6 ARC provides policy statements related to the sixth PCI DSS requirement. This requirement mandates organizations to keep the organization safe with vulnerability management and use industry standard secure development practices. All organizations will have vulnerabilities residing in software, hardware or even in the people running the business who fall victim to social engineering tactics. The organization needs to ensure that an appropriate vulnerability management program is in place to protect the network.
A vulnerability management program helps to identify and monitor vulnerabilities in the organization, categorize detected vulnerabilities to an appropriate severity, and remediate vulnerabilities to mitigate the risk. The program and the work necessary to maintain the process should be a continual process within the organization. The process should follow a documented and coordinated change control program. A change control program helps to ensure that changes to the organization minimize potential impact and the business can continue to operate without issues from changes.
Developing applications and services for use within the organization can help the business to elevate their products and services. To elevate the organization, businesses are developing applications for internal and/or external use to support the PCI related aspects of the business. However, there are secure development caveats organizations need to have integrated into the development process for PCI security requirements. Simply developing an application to support the PCI related processes can unintentionally open up the organization to potential vulnerabilities. Following industry standard secure development methodologies can help the organization to mitigate risk at the onset of the application development. Security teams can use this ARC to ensure security is a continual process throughout the organization and assist analysts to adhere with requirement 6 of PCI DSS.
Organizations can configure repositories or asset lists in order to tailor the focus of the ARC. When the ARC is added from the Tenable Security Center Feed, the appropriate assets, IP addresses, or repositories can be specified. Assigning one of the options to the ARC will update all filters in the policy statements. By creating static or combination asset lists that include all systems in the Cardholder Data Environment (CDE), each policy statement can be filtered to display results directly related to ongoing PCI security. Using an asset list filter will also allow traffic into and out of the CDE to be monitored. In order to accurately measure an organization’s PCI security posture, asset lists need to be applied as filters to provide results focused on the CDE.
This ARC is available in the Tenable Security Center Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The ARC can be easily located in the Tenable Security Center Feed under the category Compliance. The ARC requirements are:
- Tenable Security Center
- Nessus
Tenable's Tenable Security Center provides continuous network monitoring, vulnerability identification, and PCI security monitoring. Tenable Security Center is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of PCI regulatory compliance configuration audit files. Tenable constantly analyzes information from our unique sensors, delivering continuous visibility and critical context, enabling decisive action that transforms your security program from reactive to proactive. Analysts can use this information to analyze systems to evaluate with PCI security and validate expected system configurations across the organization. Active scanning examines the devices on the systems, running processes and services, configuration settings, and vulnerabilities. With this information, analysts have greater insight to determine if supported software and systems are operating within the organization. Continually scanning the network, servers, desktops and applications helps prioritize security efforts to mitigate threats and weaknesses. With active and passive scanning, analysts can detect vulnerabilities with software and web applications to remediate or mitigate. Tenable enables powerful, yet non-disruptive, continuous monitoring of the organization to ensure vulnerabilities are available to analysts.
This ARC includes the following policy statements:
All actively and passively detected systems have been scanned in the last 14 days (6.1): This policy statement displays the ratio of detected systems that have been scanned in the last 14 days to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Systems on the network are detected both passively by NNM and actively by Nessus. All systems should be actively scanned by Nessus to ensure that all systems are properly identified and evaluated.
No systems have unpatched vulnerabilities where the remediating patch was published over 30 days ago (6.3): This policy statement displays the ratio of systems with unpatched vulnerabilities for which a patch was published over 30 days ago to all systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Vulnerabilities that remained unpatched for extended periods of time can lead to system compromise or exploitation. This policy statement will help to identify systems that have vulnerabilities with patches available for over 30 days. Unpatched vulnerabilities may be susceptible to exploitation and should be remediated quickly to improve security.
No systems have unpatched vulnerabilities where the remediating patch was published over 60 days ago (6.3): This policy statement displays the ratio of systems with unpatched vulnerabilities for which a patch was published over 60 days ago to all systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Vulnerabilities that remained unpatched for extended periods of time can lead to system compromise or exploitation. This policy statement will help to identify systems that have vulnerabilities with patches available for over two months. Unpatched vulnerabilities may be susceptible to exploitation and should be remediated quickly to improve security.
No web servers have exploitable vulnerabilities (6.4.1): This policy statement displays the ratio of exploitable web server vulnerabilities to total web server vulnerabilities. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Web server vulnerabilities can expose systems to additional risk of exploitation. This policy statement will help to monitor and identify vulnerabilities that can increase the risk to an organization. Web server vulnerabilities have a greater attack surface due to their exposure to the Internet. These exploitable vulnerabilities should be remediated quickly to improve security.
No systems have injection or input validation vulnerabilities (6.2.4): This policy statement displays the ratio of external-facing systems with injection or input validation vulnerabilities to all external-facing systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. External-facing systems are especially susceptible to malicious activity, and the potential of injection or input validation vulnerabilities dramatically increases the risk of exploitation. The number of systems with potential injection or input validation vulnerabilities should be limited and carefully monitored to ensure data security.
No systems have authentication or access control vulnerabilities (6.2.4): This policy statement displays the ratio of external-facing systems with authentication or access control vulnerabilities to all external-facing systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. External-facing systems are especially susceptible to malicious activity, and the potential of authentication or access control vulnerabilities dramatically increases the risk of exploitation. The number of systems with potential authentication or access control vulnerabilities should be limited and carefully monitored to ensure data security.
No vulnerabilities are related to Cross-Site Scripting (XSS) (6.2.4): This policy statement displays the ratio of Cross-Site Scripting (XSS) vulnerabilities to total vulnerabilities. If the policy statement is met, the result is displayed in green; otherwise, the result is displayed in red. Exploited XSS vulnerabilities can result in further compromise to systems. This policy statement will help to identify and monitor XSS vulnerabilities that could be exploited. XSS vulnerabilities should be remediated to reduce the risk of network compromise.
No vulnerabilities are related to SQL Injection (SQLi) (6.2.4): This policy statement displays the ratio of SQL Injection (SQLi) vulnerabilities to total vulnerabilities. If the policy statement is met, the result is displayed in green; otherwise, the result is displayed in red. Exploited SQLi vulnerabilities can result in further compromise to systems. This policy statement will help to identify and monitor SQLi vulnerabilities that could be exploited. SQLi vulnerabilities should be remediated to reduce the risk of network compromise.
No systems have unsupported operating systems (6.3): This policy statement displays the ratio of unsupported operating systems to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Unsupported operating systems can expose the organization to an additional risk of compromise. This policy statement will help to monitor and identify unsupported operating systems. Unsupported operating systems most often still have unresolved vulnerabilities, bugs, and other unexpected behavior. With no remediating opportunity available for these potential exploitable vulnerabilities, analysts have to mitigate the risk as best as possible. These exploitable vulnerabilities should be remediated quickly to improve security.
No systems have unsupported software (6.3): This policy statement displays the ratio of unsupported operating systems to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Unsupported software can expose the organization to an additional risk of compromise. This policy statement will help to monitor and identify unsupported software. Unsupported software most often still have unresolved vulnerabilities, bugs, and other unexpected behavior. With no remediating opportunity available for these potential exploitable vulnerabilities, analysts have to mitigate the risk as best as possible. These exploitable vulnerabilities should be remediated quickly to improve security.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success