Even the most sound security policies today present major challenges for security teams, as malware can easily evade traditional security controls, and remain undetected for weeks or months. As malware becomes more advanced, organizations may face repeated attacks, and won’t be able to take the corrective action needed to minimize the risk. This Assurance Report Card (ARC) provides the latest information on malicious processes, vulnerabilities, and other threats, which can be useful in determining whether existing security solutions are effective.
Malware attacks today have become more sophisticated than ever. As malware attacks continue to evolve, so have the delivery mechanisms used to launch malicious attacks. Devices such as removable media and mobile phones have been increasingly used to transport and propagate malware throughout a network. Organizations must be vigilant in ensuring that vulnerability scanning is performed on a regular basis. Additionally, organizations should ensure that all unauthorized portable devices are prevented from launching malicious code. This ARC aligns with the malware controls of the ISO/IEC 27002 framework, which can help to ensure that malicious code is detected and remediated in a timely manner.
As organizations continue to expand and support mobility needs, many still have inadequate security controls to protect against malware and other malicious attacks. Although BYOD policies can help to increase employee productivity, organizations can quickly lose visibility on existing devices connected to the network. Any unmanaged or unknown device can present serious risks for the organization, and serve as an entry point for malware. Organizations should review all security and risk assessment policies for any blind spots, and insufficient controls.
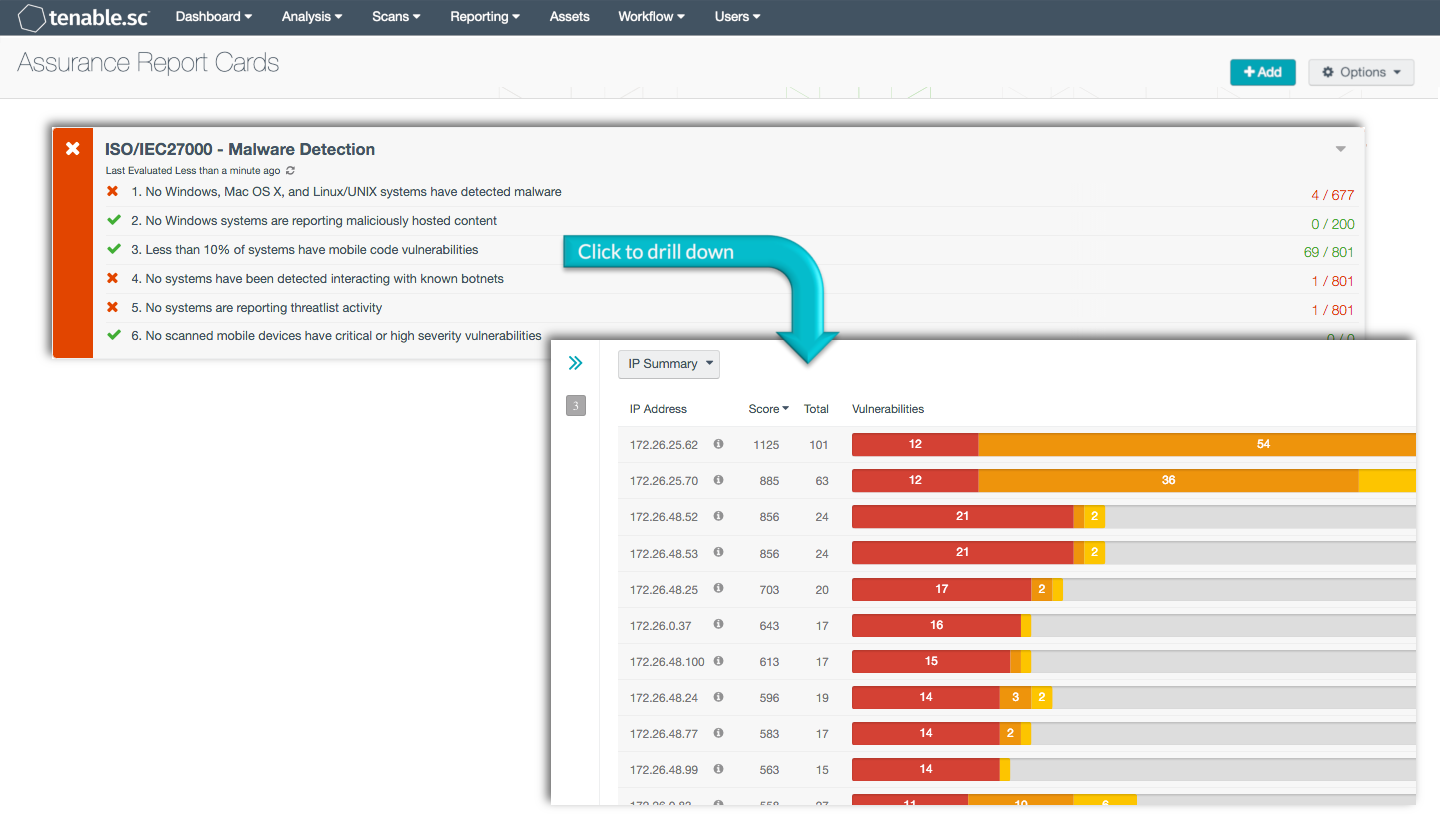
The ARC will provide information on malware and other malicious activity from systems and devices on the network. Policy statements will report on detected malware events, suspicious network traffic, network intrusions, and more. Suspicious traffic may indicate activity from malicious backdoors, intrusion attempts, and botnet communication outside the network. Additional policy statements include information on mobile and USB devices that have detected malware activity. Information provided within this ARC can be used to enhance visibility, identify risks, and eliminate gaps within existing security policies. Organizations can then take the appropriate steps needed to reduce the likelihood of a successful malware attack.
This ARC is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The ARC can be easily located in the Feed under the category Compliance. The ARC requirements are:
- Tenable.sc 5.3.2
- Nessus 8.5.1
- LCE 6.0.0
- NNM 5.9.1
Tenable.sc Continuous View (Tenable.sc CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. Nessus is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. The Nessus Network Monitor (NNM) performs deep packet inspection to enable discovery and assessment of operating systems, network devices, hypervisors, databases, tablets, phones, web servers, cloud applications, and critical infrastructure. The Log Correlation Engine (LCE) performs deep log analysis and correlation to continuously discover and track systems, applications, cloud infrastructure, trust relationships, and vulnerabilities. By integrating with Nessus, NNM, and LCE, Tenable.sc CV’s continuous network monitoring is able to detect events and vulnerabilities across the enterprise.
ARC Policy Statements:
No Windows, Mac OS X, and Linux/UNIX detected systems have detected malware: This policy statement displays the number of Windows, Mac OS X, and Linux/UNIX-based systems that have detected malware to the total number of Windows, Mac OS X, and Linux/UNIX-based systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Nessus can detect a wide variety of malware and malicious running processes. Any systems infected with malware should be further investigated by the organization. Organizations can use this policy statement to track the status of malware remediation efforts.
No Windows systems are reporting maliciously hosted content: This policy statement displays the number of Windows systems reporting maliciously hosted content to the total number of Windows systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Systems within this policy statement trigger when the md5sum of one or more processes on Windows hosts match known malware. Malicious content may indicate compromised websites that have malicious links, botnet activity, and malicious processes on Windows hosts. Any systems that have detected malware or other malicious processes should be investigated immediately by the organization to minimize security risks.
Less than 10% of systems have mobile code vulnerabilities: This policy statement displays the number of systems detected with mobile code vulnerabilities to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Systems with mobile code vulnerabilities may include outdated versions of Java, Active X, Flash, PHP, and more. Mobile code vulnerabilities can present serious risks to the organization, and should be investigated further to determine the risk.
No systems have been detected interacting with known botnets: This policy statement displays the number of systems detected interacting with known botnets to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Tenable.sc receives a daily updated list of IP addresses and domains that are participating in known botnets. Using this information, systems on the network that interact with known botnets can be detected. Any systems interacting with known botnets should be investigated immediately by the organization to minimize security risks.
No systems are reporting threatlist activity: This policy statement displays the number of systems reporting continuous activity to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Threatlist activity will report on inbound and outbound intrusions, potential data leakage, crowd surges, suspicious proxy activity, suspicious network traffic, and other suspicious host activity. This policy will alert to potential trends, revealing ongoing attacks and prevent future incidents.
No scanned mobile devices have critical or high vulnerabilities: This policy statement displays the number of scanned mobile devices infected with critical or high vulnerabilities to the total number of scanned mobile devices. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Information included within this policy statement includes scanned mobile devices that are not apart of an MDM solution. Scanned mobile devices often contain vulnerabilities that attackers can exploit. This policy can be useful in detecting and preventing unauthorized mobile devices from connecting to the network.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success