by Josef Weiss
Scanning the network for vulnerabilities to keep assets secure and intruders out is common practice. Organizations conduct periodic external scans to detect vulnerabilities, open ports and protocols. Internal scans are commonly used to identify at risk assets and provide insight into the patch management process. Microsoft Active Directory servers - a key component of many networks - contain information regarding all the objects within the domain, such as users, computers, applications, shared resources, and more. Many would not hesitate to protect the physical key for the front door, or lockbox, yet overlook an in-depth security analysis of a server in the data center.
Historically, when large data breaches are reported in the media, they are carried out by outside attackers. The reality is that insider attacks continue to make up a significant portion of data theft, and these attacks are the hardest to prevent. The increasing complexity of organizational networks and the growing interconnection of many IT dimensions, including OT, cloud, and web apps, has opened new opportunities for adversaries. To achieve lateral movement across their victims' many infrastructures, attackers now target the one system that connects everything together: Active Directory. AD is a favored target for attackers to elevate privileges and facilitate lateral movement through a network. If an external attack is successful in providing access to the inside protected network, poorly configured AD servers can provide additional privileges to a malicious actor.
Organizations also face additional challenges inside the network managing employees, contractors, consultants, guests, and other authorized users, all with varying levels of access. Insiders have advanced knowledge of organizational security practices, and know where data is stored. AD Vulnerabilities can potentially allow local attackers to escalate permissions and gain access to assets that would otherwise be restricted.
Active Directory attacks typically fall under 2 categories for 2 different motivations:
- Passwords and credentials protection.
- Privilege escalation & lateral movement prevention.
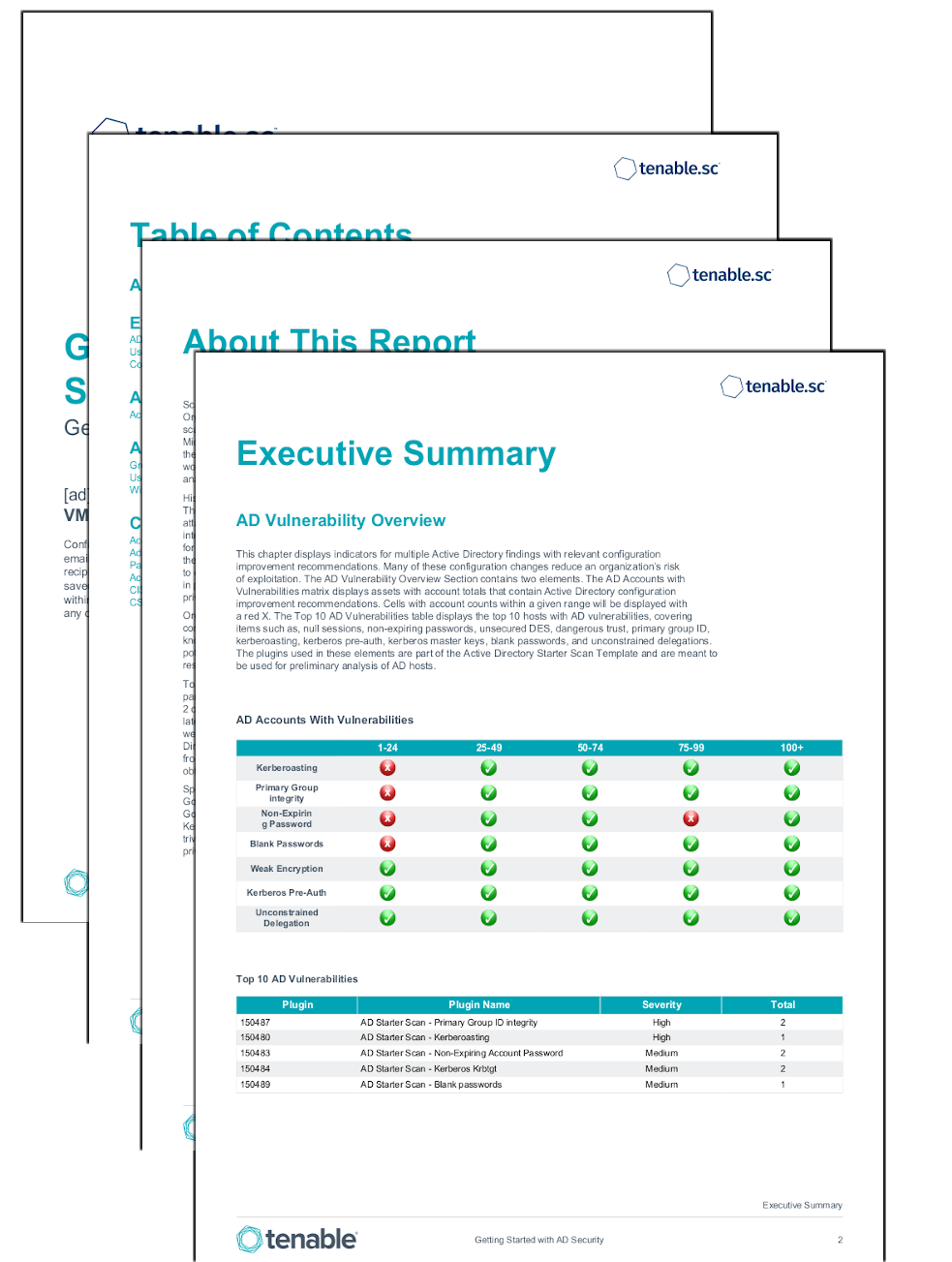
To respond to this growing threat, this report utilizes a specialized set of plugins. These plugins are part of the Active Directory Starter Scan Template and are meant to be used for preliminary analysis of AD hosts. For more information on the issues discovered by the Active Directory Starter Scan plugins, please refer to this blog post. The Active Directory Starter Scan Template contains 10 hygiene checks that were chosen for their criticality, being often exploited by attackers seeking to navigate their targets' Active Directory. These plugins focus on the two most common attack paths and take aim at preventing attackers from guessing or cracking accounts’ secrets, impersonate other users, and limit the ability for attackers to obtain more rights and to move across domains.
Specifically, this report assists organizations in the identification of potentially hard to spot attacks such as Golden Ticket attacks. Outside of legacy protocols, weak passwords, and accounts with elevated privileges, Golden Ticket Attacks are the most common attack against AD servers. Golden Ticket attacks center around Kerberos and KRBTGT (Kerberous Ticket Granting Ticket) - such as Kerberoasting - which are typically trivial to successfully launch from the inside of the network. Kerberoasting is an attack which enables privilege exploitation, furthering the ability of an attacker to move laterally in the network.
These attacks are dangerous as the attacker does not require administrative rights. An attacker can merely request a service ticket from the Domain Controller and then use password cracking tools offline to retrieve plaintext credentials from vulnerable hashes. Additionally, AD vulnerabilities that can be a benefit to attackers in this process are also identified, such as Null Sessions, Primary Group ID, Weak Encryption, and Dangerous Trust Relationships.
Tenable.sc unifies security data from across the organization, providing a comprehensive view and understanding of the organization's overall security posture. Using a diverse deployment of Nessus scanners, administrators have complete visibility into network connected assets with comprehensive vulnerability assessment coverage. When Active Directory concerns are identified, Tenable.sc quickly provides alerts via workflows and notifications, which speed up incident response and vulnerability remediation. Additionally, Tenable.ad provides a comprehensive cyber exposure determination of Active Directory hosts.
This report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessments.
The report requirements are:
- Tenable.sc 5.18.0
- Nessus 8.15.0
This report contains the following chapters:
- Executive Summary - This chapter displays indicators for multiple Active Directory findings with relevant configuration improvement recommendations. Many of these configuration changes reduce an organization’s risk of exploitation.
- Active Directory Vulnerabilities - The Active Directory Chapter provides details related to Active Directory configuration improvement recommendations. The chapter contains detailed output for each of the AD vulnerability plugins to include kerberoasting, primary group identity, non-expiring passwords, blank passwords, weak encryption, kerberos pre-auth, and unconstrained delegations.
- Account Status Chapter - The Account Status Chapter contains sections that allow for an in-depth review and audit of group memberships, users, security identifiers, and Windows Server Message Block vulnerabilities.
- Compliance Chapter - The Compliance Chapter contains sections that review Windows account compliance results. The elements display user access, least privilege, and other compliance information in areas such as password requirements, lockout policy after failed logins, and controlled use of administrative privileges.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success