by David Schwalenberg
September 23, 2015
Monitoring web activity for known threats or other related vulnerabilities is often difficult for security operations. Many organizations have content filters, anti-virus gateways, and intrusion detection/prevention systems; but security analysts often times do not have direct access to the logs for these systems. SecurityCenter Continuous View (CV) allows the operations team to monitor web activity via sniffing DNS requests and monitoring related traffic.
Monitoring DNS activity can be accomplished by setting the Passive Vulnerability Scanner (PVS) to monitor communication paths between clients and DNS servers. Additionally the DNS server can be configured send logs to the Log Correlation Engine (LCE). LCE then creates summary events of DNS queries and the information can be logged and analyzed. The dashboard uses the Domain_Summary, Domain_Failure_Summary, and SSL_Cert_Summary events, which all provide lists of domains accessed. Searches are performed within these events to find specific domains of interest. Each summary event for a given IP address provides the domains accessed by that IP address since the last such event for that system (which may be as often as hourly). The dashboard components can be altered as needed to add or remove domains of interest. If failed attempts to access domains do not need to be tracked, remove the Domain_Failure_Summary event from the filters in the components.
There are two key items to remember when performing DNS analysis. First, the detection of a DNS query for a site does not necessarily mean that the site was visited. The event can be the result of site-related icons or thumbnails being displayed on other web pages. Second, this dashboard relies on PVS detections being forwarded to the LCE. Make sure that the PVS is configured to send syslog messages to the LCE: in Configuration > PVS Settings > Syslog, include the LCE host (with port 514) in the Realtime Syslog Server List. The LCE listens for syslog messages by default.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Monitoring.
The dashboard requirements are:
- SecurityCenter 4.8.2
- PVS 4.4.0
- LCE 4.6.0
Tenable provides continuous network monitoring to identify vulnerabilities, reduce risk, and ensure compliance. PVS provides deep packet inspection to continuously discover vulnerabilities and Indicators of Compromise (IOC) traveling the wire. LCE correlates real-time events, such as DNS queries, and then performs analysis to discover vulnerabilities and IOC. LCE also has the capability to discover users, operating systems, network devices, hypervisors, databases, tablets, phones, web servers, and other critical infrastructure. SecurityCenter CV allows for the most comprehensive and integrated view of network health.
For a procedure to get sorted lists of websites accessed, see Use SecurityCenter to Obtain a List of Websites Accessed.
Listed below are the included components:
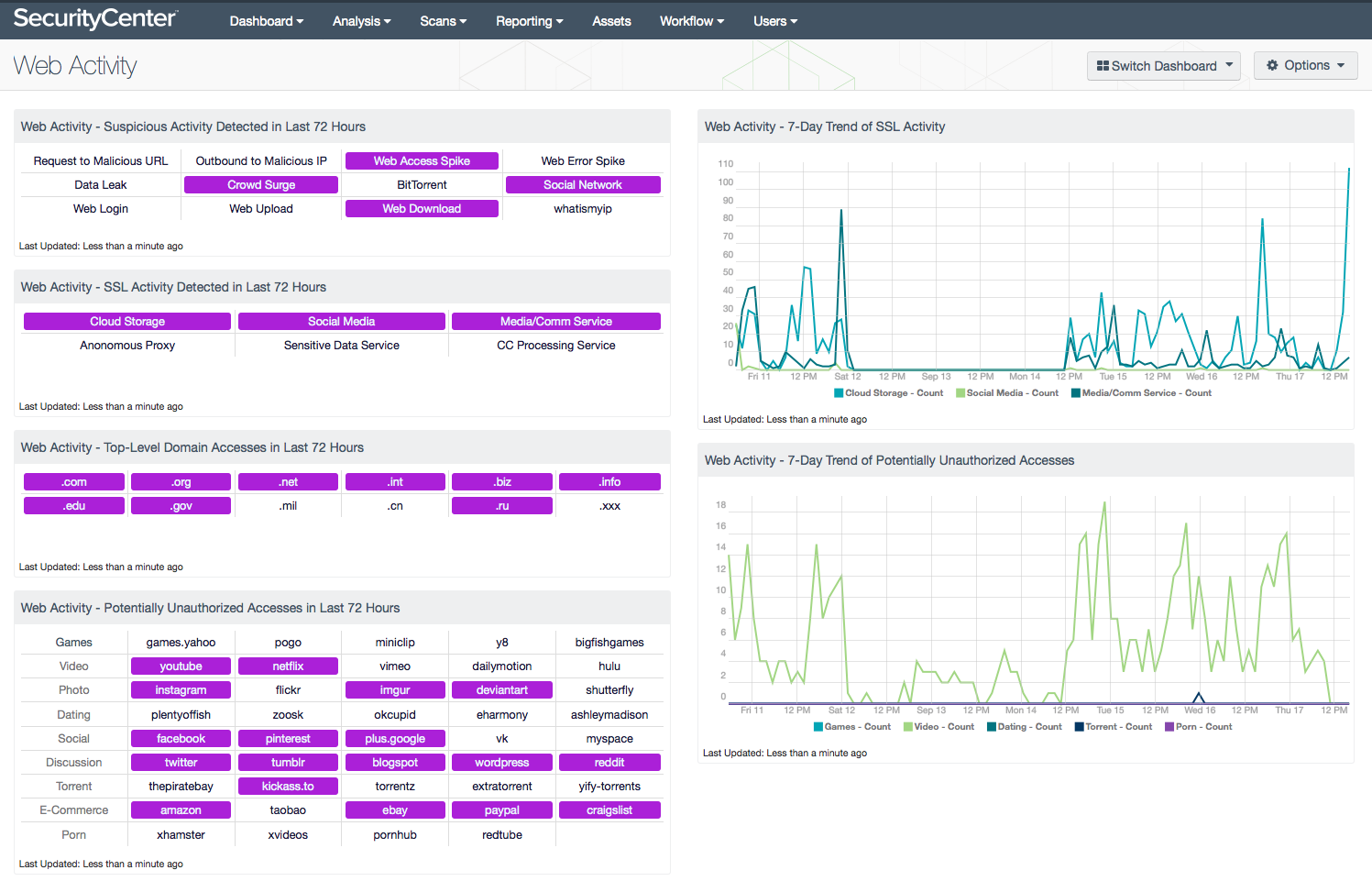
- Web Activity - Suspicious Activity Detected in Last 72 Hours - This matrix presents detections of potentially suspicious web activity that have occurred in the last 72 hours. Red indicators signify activity of high severity; orange indicators signify activity that is less severe, but warrants further investigation.
- Web Activity - SSL Activity Detected in Last 72 Hours - This matrix presents informational indicators of SSL events that have occurred in the last 72 hours, including access to cloud file storage, access to social media (such as Facebook or Twitter), access to media/communication services (such as Netflix or Skype), access to anonymous proxy services (which allow anonymous access to the Internet), access to services commonly used for sensitive data, and access to services used for processing credit card transactions.
- Web Activity - Top-Level Domain Accesses in Last 72 Hours - This matrix presents informational indicators of top-level domains of interest accessed in the last 72 hours. This component can be altered to add or remove top-level domains of interest as needed. These indicators use the Domain_Summary, Domain_Failure_Summary, and SSL_Cert_Summary events, which all provide lists of domains accessed; searches are performed within these events to find specific domains of interest. Each summary event for a given IP address provides the domains accessed by that IP since the last such event for that IP (which may be as often as hourly). This component can be altered to add or remove domains of interest as needed. If failed attempts to access domains do not need to be tracked, remove the Domain_Failure_Summary event from the filter for these indicators. Note that the PVS-DNS_Top_Level_Domain_Queries event is not used here, as its output will not necessarily be limited to the last 72 hours.
- Web Activity - Potentially Unauthorized Accesses in Last 72 Hours - This matrix presents warning indicators of popular but potentially unauthorized domains of interest accessed in the last 72 hours. This component can be altered to add or remove domains of interest as needed. These indicators use the Domain_Summary, Domain_Failure_Summary, and SSL_Cert_Summary events, which all provide lists of domains accessed; searches are performed within these events to find specific domains of interest. Each summary event for a given IP address provides the domains accessed by that IP since the last such event for that IP (which may be as often as hourly). This component can be altered to add or remove domains of interest as needed. If failed attempts to access domains do not need to be tracked, remove the Domain_Failure_Summary event from the filter for these indicators.
- Web Activity - 7-Day Trend of SSL Activity - This chart presents a 7-day trend graph of various SSL events, including access to cloud file storage, access to social media (such as Facebook or Twitter), and access to media/communication services (such as Netflix or Skype).
- Web Activity - 7-Day Trend of Potentially Unauthorized Accesses - This chart presents a 7-day trend graph of accesses to popular but potentially unauthorized domains, including several games, video, dating, torrent, and porn sites. This component can be altered to add or remove domains of interest as needed. This chart uses the Domain_Summary, Domain_Failure_Summary, and SSL_Cert_Summary events, which all provide lists of domains accessed; searches are performed within these events to find specific domains of interest. Each summary event for a given IP address provides the domains accessed by that IP since the last such event for that IP (which may be as often as hourly). This component can be altered to add or remove domains of interest as needed. If failed attempts to access domains do not need to be tracked, remove the Domain_Failure_Summary event from the filter in each series.