by Stephanie Dunn
December 8, 2016
Protecting the network against threats requires a comprehensive and continuous approach. Organizations have thousands of endpoints that can be difficult to manage effectively. Misconfigurations in any one these endpoints will leave security gaps that place critical systems at risk. This dashboard covers key concepts within the ITSG-33 guide that focuses on data protection, discovery of systems with sensitive data, and detection of data leakage.
The Communications Security Establishment Canada (CSEC) developed a series of guidelines for security practitioners in managing information technology (IT) security risks for Government of Canada (GC) information systems. The Information Technology Security Guidance Publication 33 (ITSG-33), IT Security Risk Management: A Lifecycle Approach provides a comprehensive set of security controls that can be used to support a wide variety of business requirements. To support interoperability needs, the ITSG-33 guide is consistent with controls published in the U.S. National Institute of Standards and Technology (NIST) Special Publication 800-53. Data presented within this dashboard aligns with ITSG-33 security controls that support the protection of information systems, and the transmission of data within those systems. This dashboard aligns with the following controls:
- Boundary Protection (SC-7)
- Transmission Confidentiality and Integrity (SC-8)
- Cryptographic Protection (SC-13)
- Protection of Information at Rest (SC-28)
- Media Protection (MP-Family)
Protecting organizational data is a critical part of any security program, as this information can be easily exploited if left unprotected. Attackers can use this information to steal credit card data, exploit customer information, obtain company trade secrets, and more. Employees can also inadvertently leak data through sending unencrypted emails, transferring unencrypted data on portable devices, and failure to properly protect data at rest. This dashboard assists security teams in monitoring network endpoints for data leakage, identifying systems with sensitive data, and detecting systems at risk for information disclosure.
Vulnerabilities related to privilege escalation, information disclosure, and man-in-the-middle attacks will highlight systems at risk for data disclosure. Analysts will be able to monitor services and devices in use on the network that could be used to disclose confidential information. Event data will focus areas of concern, which can assist in identifying security controls that may have been initially overlooked by security teams. Using this dashboard, organizations will be able to better protect their data, and strengthen existing security controls.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Tenable.sc 5.4.1
- Nessus 8.5.1
- LCE 6.0.0
- NNM 5.9.0
- complianceData
Tenable's Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring solution that will assist in protecting organizational data. Tenable.sc CV is continuously updated with information about advanced threats, zero-day vulnerabilities, and regulatory compliance data. Active scanning periodically examines systems to determine vulnerabilities and compliance concerns associated with information disclosure. Agent scanning enables scanning and detection of vulnerabilities on transient and isolated devices. Passive listening provides real-time discovery of vulnerabilities on operating systems, protocols, network services, wireless devices, web applications, and critical infrastructure. Host data and data from other security products is analyzed to monitor the network for data leakage and systems at risk for data disclosure. Tenable.sc CV provides an organization with the most comprehensive view of the network and the intelligence needed to protect critical systems and data on the network.
The following components are included within this dashboard:
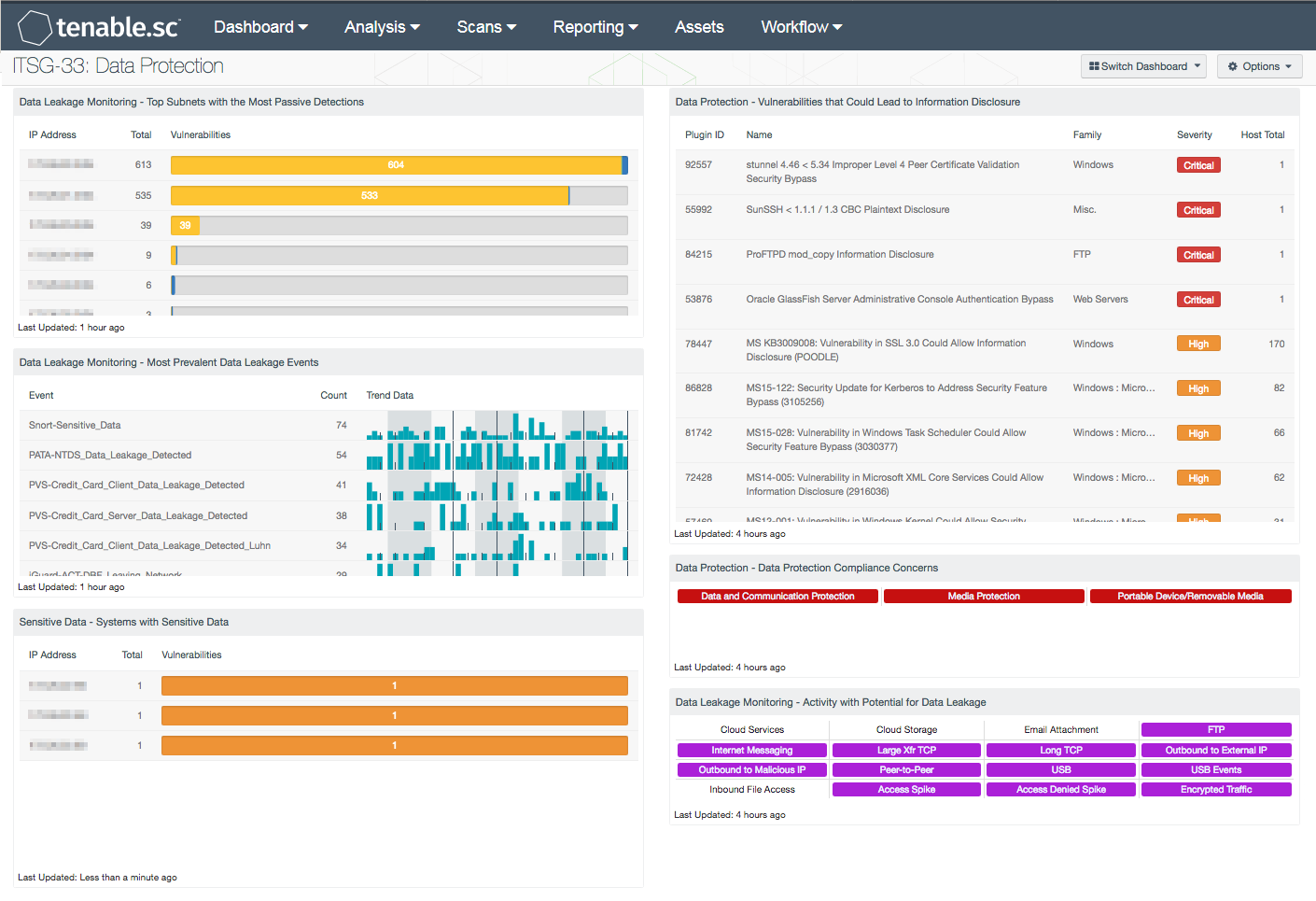
- Data Leakage Monitoring - Top Subnets with Data Leakage Detected: This table presents the top Class C subnets with the most passive detections of data leakage. These passive detections are vulnerabilities reported by the Nessus Network Monitor (NNM) in the “Data Leakage” plugin family. The list is ordered so that the subnet with the highest number of detected data leakage activity is at the top. Activity highlighted within this component may include leakage of user credentials, Social Security numbers, file uploads, clear text transmission of credit card numbers, and more. A count of detections and a bar graph indicating the severity of the detections are given for each subnet.
- Data Leakage Monitoring - Top 10 Most Prevalent Data Leakage Events (Last 72 Hours): This table presents the most prevalent logged data leakage events in the last 72 hours. The logged events are reported by the Log Correlation Engine (LCE) under the “data-leak” event type, and include events forwarded via syslog from NNM. Activity reported from systems and services that have detected sensitive data, confidential information, and credit card leakage is included within this component. Data is sorted by the highest number of events at the top, and includes a trend graph for each event.
- Sensitive Data - Systems with Sensitive Data: This component presents a summary of systems with files that contain sensitive data. In order to identify systems with sensitive data, audit files from the Windows and Unix File Content Template folders are required. Information presented within this component will detect systems with credit card data, Social Security numbers, corporate source code, and other forms of Personally Identifiable Information (PII) stored on them. Systems with the highest number of detections of sensitive data stored on them are at the top of the list. Analysts can modify the component to include additional or specific information per organization requirements.
- Data Protection - Vulnerabilities that Could Lead to Information Disclosure: This component presents a list of actively and passively detected vulnerabilities that could lead to data disclosure. Vulnerabilities at all severity levels except Informational are included. The keywords cover disclosures, cryptographic issues, man-in-the-middle vulnerabilities, and weak authentication concerns. Clicking on the Browse Component Data icon will bring up the vulnerability analysis screen to allow further investigation of the vulnerabilities. In the analysis screen, setting the tool to IP Summary will display the systems on which the vulnerabilities are present. This component is used to strengthen security controls and better protect data.
- Data Protection – Data Protection Compliance Concerns: This component presents indicators that highlight compliance concerns associated with data, communication, and media protection. Red indicators are triggered when one or more compliance concerns have failed the compliance check or are out of the compliance range. Clicking on the indicator will bring up the vulnerability analysis screen to display details on the compliance concerns. Compliance issues highlighted within this component may indicate services that need to be disabled, permission changes, and other system hardening controls. The data should be reviewed by security teams to determine the level of risk to the organization.
- Data Leakage Monitoring - Activity with Potential for Data Leakage: This component presents indicators for activity detected on the network that has the potential for data leakage. The indicators are based on events logged in the last 72 hours and on actively and passively detected vulnerabilities. Indicators are included for such things as cloud interaction, outbound traffic to external IP addresses, peer-to-peer file sharing vulnerabilities, and USB usage. A purple indicator highlights a vulnerability/event detection. Clicking on a highlighted indicator will bring up the analysis screen to display details on the vulnerabilities/events. In the analysis screen, setting the tool to IP Summary will display the systems on which the vulnerabilities/events are present. This component can be used to investigate the potential for data leakage.