by Megan Daudelin
May 18, 2016
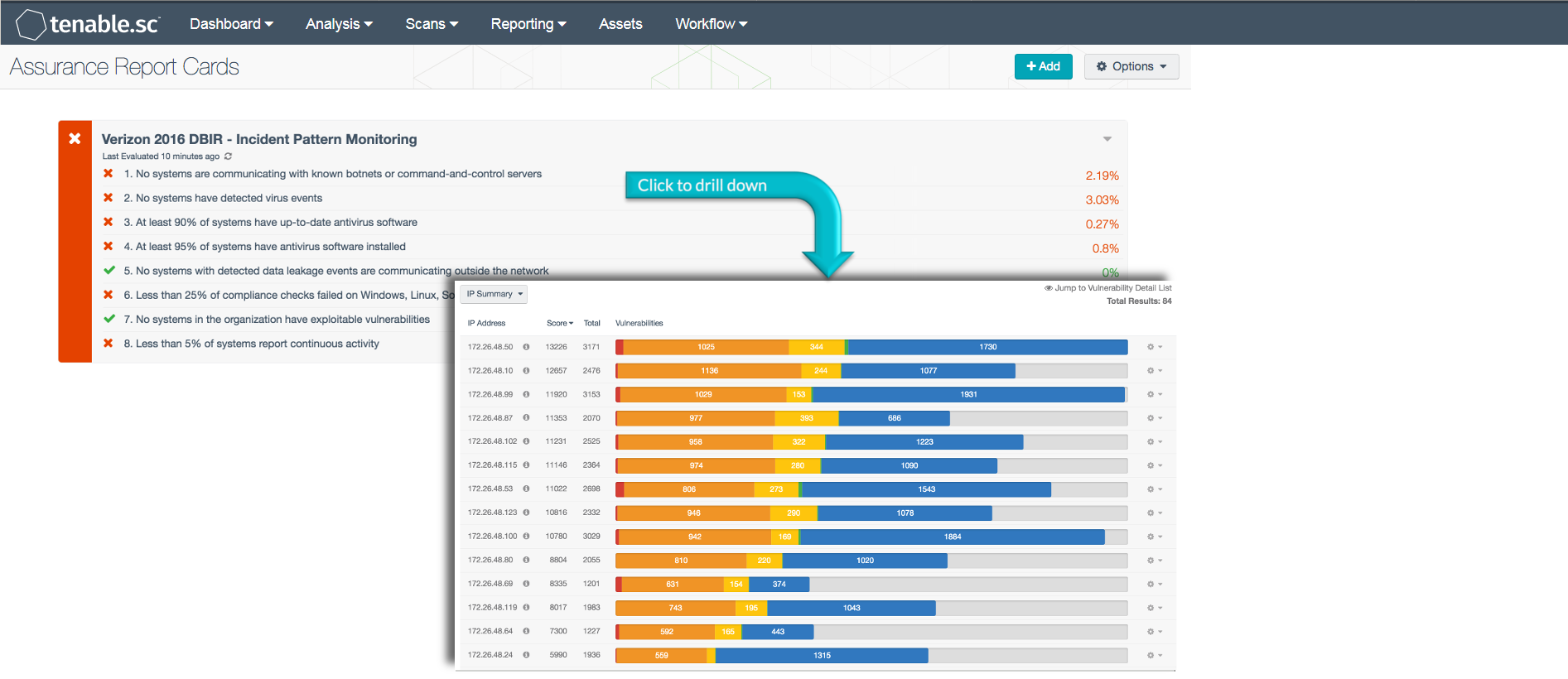
The Verizon Data Breach Investigation Report (DBIR), first published in 2008, is an annual publication that analyzes information security incidents from public and private organizations, with a focus on data breaches. Data breaches continue to have a major financial impact on organizations, as well as an impact on their reputations. Tenable Network Security offers dashboards and Assurance Report Cards (ARCs) that organizations can use to check themselves against the common threats described in the Verizon DBIR. As in previous years, the 2016 DBIR notes that a vast majority of all attacks fall into a few basic patterns. Throughout this and past years’ reports suggestions are given for monitoring the network for each of these patterns. Based on best practices described in the DBIR, the Incident Pattern Monitoring ARC can assist an organization in monitoring their network for indications of common attack patterns and thus reduce the chances of a data breach.
Failing to monitor a network for vulnerability and patch management leads to a greater risk of compromised systems. Employing a multi-layered defense strategy across all endpoints provides the best protection against intrusions or attacks. Internet facing assets, including web servers and VPNs, need to be monitored to ensure that unauthorized users do not gain access to network resources. Systems must be adequately protected by antivirus so that critical systems are not left vulnerable to intrusions or attacks. Exploitable vulnerabilities and data leakage events must be addressed so that additional security risks are not introduced into the network. Organizations that do not continuously monitor and secure network defenses will not be able to respond or defend network assets effectively.
This ARC assists organizations in improving security and network defense controls. Policy statements included within this ARC report on systems that have detected intrusion or botnet activity, data leakage events, or outdated antivirus software. Additional policy statements report on continuous activity, compliance checks, and virus events. Having complete visibility of network security allows organizations to proactively respond to threats, mitigate vulnerabilities, and take preventative measures before any serious damage occurs.
The information provided in this ARC provides a baseline to measure the effectiveness of an organization's information security policies and whether the current policies being enforced are effective. The ARC policy statement parameters are guides that can be customized as necessary to meet organizational requirements.
This ARC is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Security Industry Trends.
The dashboard requirements are:
- Tenable.sc 5.3.1
- Nessus 8.5.1
- LCE 6.0.0
- NNM 5.9.0
Tenable.sc Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. Tenable.sc is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. The Nessus Network Monitor (NNM) performs deep packet inspection to enable discovery and assessment of operating systems, network devices, hypervisors, databases, tablets, phones, web servers, cloud applications, and critical infrastructure. The Log Correlation Engine (LCE) performs deep log analysis and correlation to continuously discover and track systems, applications, cloud infrastructure, trust relationships, and vulnerabilities. By integrating with Nessus, NNM, and LCE, Tenable.sc CV’s continuous network monitoring is able to detect events and vulnerabilities across the enterprise.
The following policy statements are included in this ARC:
No systems are communicating with known botnets or command-and-control servers: This policy statement displays the ratio of systems detected interacting with known botnets to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Tenable.sc receives a daily updated list of IP addresses and domains that are participating in known botnets. Using this information, systems on the network that interact with known botnets can be detected. Any systems interacting with known botnets should be investigated immediately by the organization to minimize security risks.
No systems have detected virus events: This policy statement displays the ratio of systems with virus-related activity to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Activity related to viruses can be indicative of successful or attempted infections. This policy statement helps identify systems that may be infected. Any systems with virus-related events detected should be investigated to determine whether remediation is required.
At least 90% of systems have active and up-to-date antivirus software and definitions: This policy statement displays the ratio of systems with active and up-to-date antivirus protection to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. All systems should have active and up-to-date antivirus software installed to protect against malware infections. Organization can use this information to identify and resolve antivirus software issues on systems.
At least 95% of systems have antivirus software installed: This policy statement displays the ratio of systems with antivirus software installed to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. All systems should have active and up-to-date antivirus software installed to protect against malware infections. Systems without antivirus protection or with outdated software should be reconfigured to ensure that current antivirus software is installed, running, and able to receive updates. Organization can use this information to identify and resolve antivirus software issues on systems.
No systems with data leakage events communicate outside the network: This policy statement displays the ratio of systems that have reported data leakage events and communicate outside the network to all systems with data leakage events. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Data leakage events from systems that are communicating outside the network could be indicative of an intrusion or other malicious activity. Such systems should be investigated immediately to ensure that the outside communication is not exfiltrating sensitive data from the network.
Less than 25% of compliance checks failed on Windows, Linux, Solaris, and Mac OS X machines: This policy statement displays the ratio of failed to total compliance checks across Windows, Linux, Solaris and Mac OS X machines. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. This policy statement will help an organization identify non-compliant systems, which can help to address outstanding compliance issues.
No systems in the organization have exploitable vulnerabilities: This policy statement displays the ratio of systems with exploitable vulnerabilities to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Systems with exploitable vulnerabilities can expose the network to increased risk of malicious activity and should be patched.
Less than 5% of systems report continuous activity: This policy statement displays the ratio of systems reporting continuous activity to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Continuous activity is activity that occurred over a long period of time. The activity may be legitimate, or may be activity such as port scanning, server issues, repeated login failures, or potential malware activity. The organization should further investigate any systems with continuous activity.