Hidden weaknesses in unpatched Java installations expand the organizational attack surface and expose the environment to severe operational disruptions. Visualizing impacted assets allows the organization to grasp how unmanaged applications increase overall risk exposure. A resilient defense posture requires continuous awareness of deployed infrastructure to prevent adversaries from exploiting network vulnerabilities. The Java Visibility and Exposures report resolves these challenges by transforming complex scanning data into accessible visual formats, guiding the risk manager to proactively identify hidden flaws and secure vulnerable assets.
A strong software asset management program serves as the foundation for identifying unauthorized or end-of-life applications across the network. Without a robust software asset inventory, the security operations team cannot properly evaluate network health. The report enables the risk manager to map out deployed applications, revealing potential blind spots within the infrastructure. Mapping such installations ensures the organization proactively identifies unsupported environments where vendors no longer supply security patches. Modern adversaries frequently leverage artificial intelligence to exploit unmanaged cyber risks, meaning accurate visibility into the asset landscape remains paramount for preventing unauthorized access.
Once assets are identified, prioritizing risk effectively ensures the security operations team addresses the most critical Java vulnerabilities first. Relying solely on traditional static scoring often creates overwhelming workloads. Conversely, utilizing dynamic Vulnerability Priority Ratings (VPR) focuses organizational resources on exposures associated with active threat intelligence and the highest likelihood of exploitation. Addressing high-risk exposures proactively prevents attackers from launching successful campaigns against vulnerable infrastructure. Implementing a robust vulnerability management strategy guided by threat intelligence ensures maximum risk reduction and creates a strengthened security posture.
Identifying and mapping network exposures empowers the risk manager to direct remediation efforts across affected subnets and individual host environments. Cybersecurity has evolved into a global security imperative, requiring a strategic shift toward risk-based, outcome-focused governance that elevates cyber risk discussions to the boardroom. By targeting the highest-priority threats, the organization can neutralize Server-Side Request Forgeries (SSRF) in the Java transport layer handshakes, before they can be exploited to disrupt operations. Resolving highly targeted vulnerabilities efficiently builds collective defense capabilities. Mastering detailed network visibility ultimately strengthens organizational security maturity and reduces overall cyber exposure.
Chapters
- Executive Summary: This chapter allows the risk manager to quickly identify and analyze current Java exposures across the network. Understanding how the attack surface sustains impact from assets with Java installed remains essential for a proactive defense, especially since threat actors now frequently use machine learning tools to uncover blind spots. By transforming complex scanning data into accessible visual formats, the chapter helps security leaders visualize the true impact of existing exposures. Provided insights guide the security operations team to prioritize remediation efforts effectively. Establishing a comprehensive exposure management practice guarantees the enterprise shields sensitive information while maintaining a resilient defense posture against evolving threats.
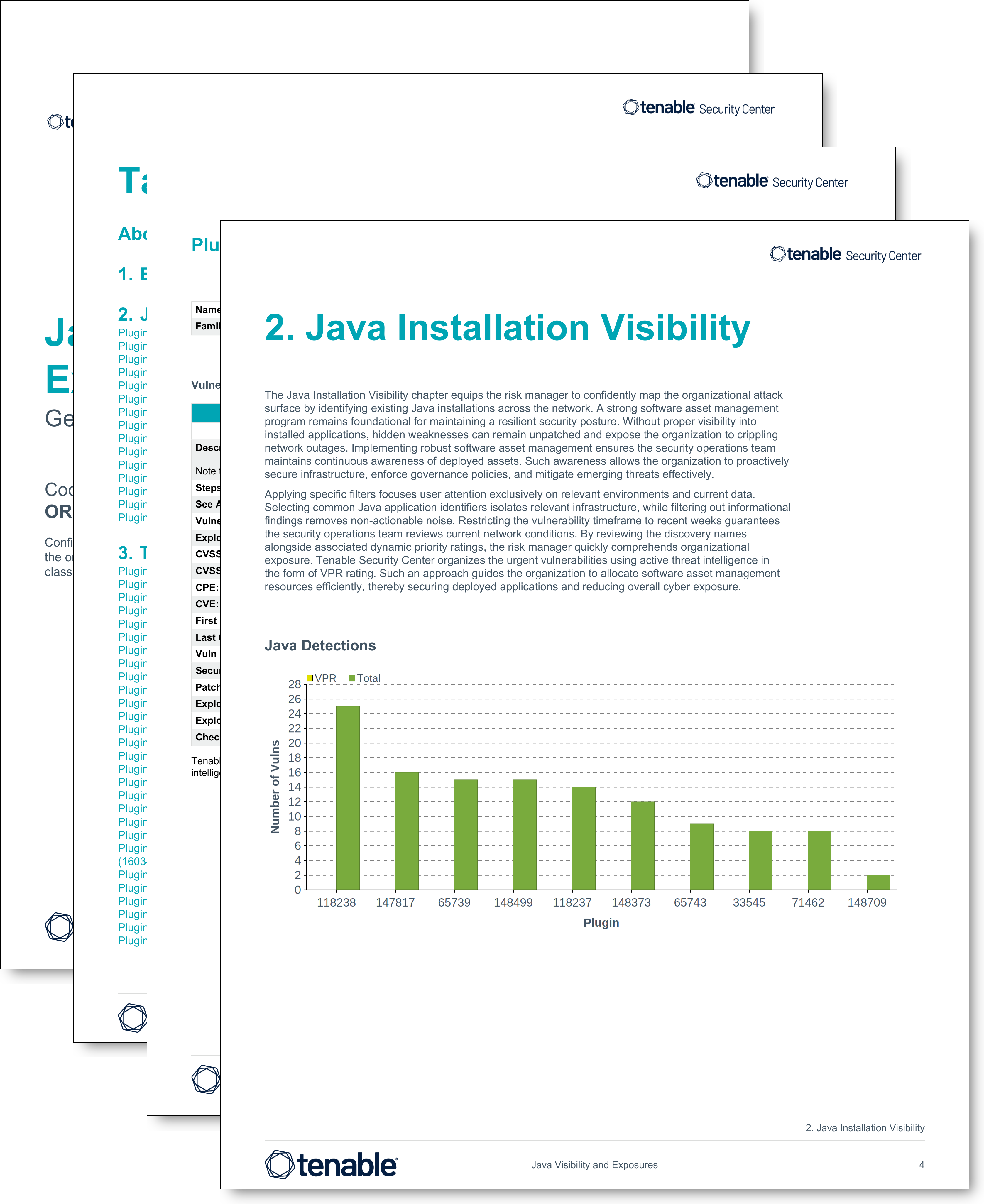
- Java Installation Visibility: This chapter equips the risk manager to confidently map the organizational attack surface by identifying existing Java installations across the network. A strong software asset management program remains foundational for maintaining a resilient security posture. Without proper visibility into installed applications, hidden weaknesses can remain unpatched and expose the organization to crippling network outages. Implementing robust software asset management ensures the security operations team maintains continuous awareness of deployed assets. Such awareness allows the organization to proactively secure infrastructure, enforce governance policies, and mitigate emerging threats effectively.
- Top Java Exposures Sorted by VPR: This chapter assists the risk manager to effectively prioritize mitigation efforts across the network. Utilizing CVSS base risk scores frequently buries security analysts under unactionable data. Conversely, applying risk-based prioritization guides security personnel to address weaknesses with the highest probability of exploitation. Addressing high-risk exposures proactively prevents adversaries from leveraging hidden weaknesses, such as Server-Side Request Forgery flaws in cryptographic handshakes, to launch devastating cyberattacks. Executing an intelligence-driven remediation workflow allows the business to rapidly mitigate critical flaws.
- Unsupported Versions of Java: This chapter guides the risk manager to confidently identify end-of-life installations across the network. Locating legacy software is a critical step in building a hardened defense because vendors no longer release security patches for outdated products. Without regular updates, hidden weaknesses remain unpatched and may expose the organization to crippling attacks. Today's attackers routinely deploy automated scripts to target neglected endpoints. To mitigate associated risks, the security operations team must continuously monitor the attack surface and upgrade legacy installations to actively supported versions. Implementing robust vulnerability management practices guided by advanced scoring algorithms direct attention to the most pressing and actionable dangers, ensuring a proactive defense.
- Hosts with the Java Vulnerabilities: This chapter enables the risk manager to comprehend the organizational attack surface by mapping Java installations across network assets. An effective vulnerability lifecycle strategy is essential for sustaining a robust defense. Unmanaged applications create cyber risk, exposing the organization to critical system failures. Visualizing affected assets allows the security operations team to maintain continuous awareness of network health and assess how severe flaws impact individual host environments. Implementing robust software asset management ensures the organization proactively secures infrastructure and mitigates emerging threats guided by dynamic predictive ratings.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success