by Josef Weiss
One of the common questions often asked of the IT team is “how many systems are missing patches and how many patches are missing on each system?” This dashboard uses the “Patch Report” plugin and organizes the current patch status for systems scanned with credentials. The IT team can now easily communicate the specific systems with missing patches to executives.
The Nessus "Patch Report" plugin (66334) elegantly summarizes all of the missing patches and general remediation actions required to remediate the discovered vulnerabilities on a given host. Instead of counting the number of vulnerabilities, the plugin lists applications that need to be upgraded. The approach is not only much easier for IT administrators to consume, but the count of applications provides a measure of how much "work" is required to secure a system.
The dashboard provides risk guidance using the “Remediation Summary” tool. This tool works by employing a concept called “top patch”. Tenable Security Center uses proprietary technology to identify a chain of patches. The first patch in the chain is called the “top patch”. If the “top patch” is applied, all subsequent vulnerabilities will also be remediated at the same time. Using both the Remediation Summary tool and “Patch Report” plugin, the organization can better plan remediation efforts.
The dashboard and its components are available in the Tenable Security Center Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the Tenable Security Center Feed under the category Executive. The dashboard requirements are:
- Tenable Security Center
- Nessus
- This dashboard requires “Full Text Search” to be enabled for each analyzed repository.
Please note the "Full Text Search" option must be enabled for the repository to support the trending component.
Tenable Security Center has the ability to identify all discoverable vulnerabilities, eliminating blind spots. Tenable detects missing patches, incorrect configurations, lapsed defenses, incomplete monitoring and network intruders—so you can mitigate them. Tenable Security Center can show risk across all systems, enabling informed decisions. Tenable’s approach to continuous monitoring reaches across cloud, virtual, mobile and traditional systems and measures attack vectors in each of these domains. Tenable Security Center provides a unique combination of detection, reporting, and pattern recognition utilizing industry recognized algorithms and models. By providing that single point of data collection, Tenable.sc enables sharing of vulnerability scanning results across the technical groups and business owners. Tenable.sc is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits.
Components
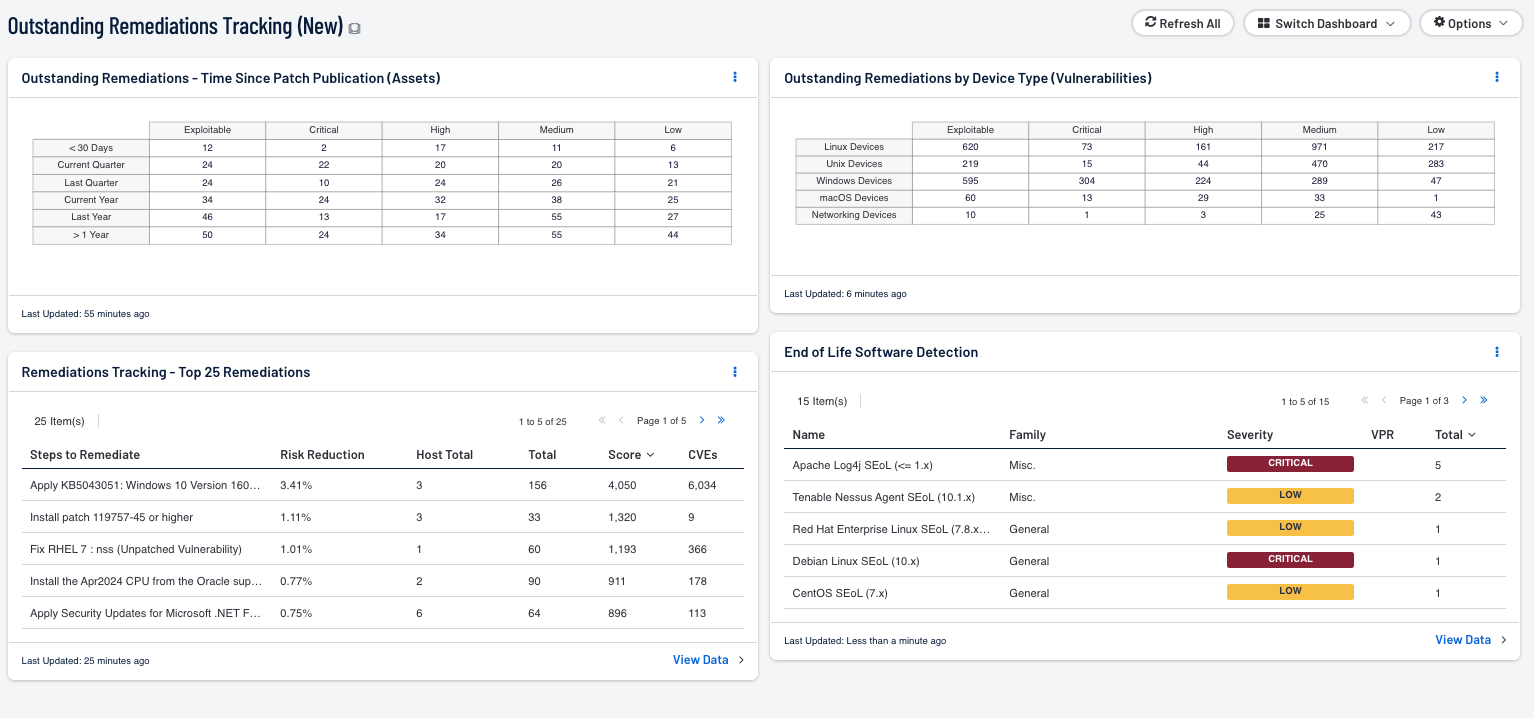
Remediations Tracking - Top 25 Remediations: This component provides the top 25 remediation actions that can be taken to reduce overall risk. The table is sorted using vulnerability weight scores, which are calculated differently for each organization. To determine score weights, login with the admin account, edit your organization and then select “Analysis”. In the upper right hand corner, there are four scores, one for each severity level. The default scores are: critical = 40, high = 10, medium = 3 and low = 1. The vulnerability weight helps to determine a fully calculated score used in risk analysis.
The Outstanding Remediations - Time Since Patch Publication (Assets) matrix displays the total count of missing patches across the environment. The matrix is comprised of five columns. The first column provides a count of the vulnerabilities that are exploitable, and the last four columns provide counts of vulnerabilities based on Vulnerability Priority Rating (VPR) levels. VPR scores are displayed as column headers in traditional severity text. Critical represents VPR 9-10, High represents VPR 7-8.9, Medium represents VPR 4-6.9, and Low represents VPR 0.1-3.9. Each row filters the vulnerabilities based on the patch publication date of less than 30 days ago, Current Quarter, Last Quarter, Current Year, Last Year, and greater than 365 Days.
The End of Life Software Detection table displays a list of software that is no longer supported by the vendor. The table is sorted by the count column, which lists a count of the total number of assets affected by the unsupported software package. The filter used is for Plugin Name equals Unsupported. Tenable recommends that assets found here be upgraded to a higher supported version as soon as possible, since vendors no longer list active vulnerabilities for end-of-life software.
The Outstanding Remediations by Device Type (Vulnerabilities) matrix displays the total count of missing patches by device type. The matrix is comprised of five columns. The first column provides a count of the vulnerabilities that are exploitable, and the last four columns provide counts of vulnerabilities based on Vulnerability Priority Rating (VPR) levels. VPR scores are displayed as column headers in traditional severity text. Critical represents VPR 9-10, High represents VPR 7-8.9, Medium represents VPR 4-6.9, and Low represents VPR 0.1-3.9. There is a row present which groups devices by type, such as Linux, Windows, or macOS devices. Counts present in each cell represents the number of vulnerabilities present for the device group and VPR score.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success