Endpoint applications proliferate across enterprise infrastructure without centralized oversight, creating blind spots that leave organizations vulnerable to attack. Risk Managers lack comprehensive visibility into which software versions operate on endpoints, making prioritization decisions difficult when application data remains fragmented across disconnected systems. Security Operations Teams consume excessive time gathering basic inventory information rather than executing remediation work that reduces actual exposure. The Security Center Dashboard helps by consolidating application visibility and vulnerability findings across critical software categories into a unified platform that enables data-driven prioritization based on deployment prevalence and exploitation likelihood.
Application inventory data flows into dedicated components that organize software by functional category, including management tools, productivity applications, database components, and other categories. Each category receives parallel treatment through paired components showing both deployment distribution and associated security exposures ranked by organizational reach. Security Operations Teams leverage deployment prevalence data to distinguish between isolated installations and widespread software deployments that affect large segments of the infrastructure. Desktop support teams coordinate upgrade campaigns using inventory intelligence that reveals version sprawl and identifies endpoints running unauthorized or outdated software.
Vulnerability prioritization extends beyond traditional severity metrics by incorporating Vulnerability Priority Rating (VPR) scores that assess exploitation likelihood based on real-world threat intelligence and attacker behavior patterns. Risk Managers evaluate which exposures warrant immediate attention by examining both the technical severity and the actual deployment count across the infrastructure. Security Operations Teams distinguish between vulnerabilities affecting three endpoints versus three thousand endpoints, directing effort toward findings with multiplicative organizational impact. Application owners collaborate with security teams using exposure rankings to understand dependencies and coordinate testing windows before patches deploy to production environments. The dashboard reduces resource waste on vulnerabilities affecting software no longer present in the environment or previously addressed through formal risk acceptance processes.
Unsupported software surfaces through specialized detection logic that identifies applications operating beyond vendor maintenance lifecycles, highlighting infrastructure segments vulnerable to unpatched exploits. Management and monitoring agents receive dedicated visibility components that enable Risk Managers to verify coverage of security tooling across the asset base and identify gaps where protective controls have failed to deploy. Browser vulnerabilities demand prioritized attention given the role web applications play as initial access vectors in phishing campaigns and drive-by download attacks targeting employees. Collaboration and productivity software exposures affect business-critical tools that process sensitive communications and intellectual property, requiring coordinated patching that balances security requirements against operational continuity. VPN client vulnerabilities introduce remote access risks that could enable adversaries to bypass perimeter defenses and establish persistent footholds within the internal network.
Database exposures receive focused analysis given the sensitive nature of data assets these systems typically protect and the severe consequences following successful database compromise. Java vulnerabilities require careful remediation planning that considers cascading impacts across dependent applications throughout the portfolio. The organization benefits from consolidated exposure intelligence that eliminates duplicate scanning efforts and provides security teams with an authoritative source for application vulnerability data. Risk acceptance workflows integrate directly with assessment findings, allowing Risk Managers to document business justifications when applications must remain operational despite known vulnerabilities due to compatibility constraints or operational dependencies. Desktop administrators reference the paired visibility and exposure components when planning decommissioning activities for obsolete software or standardization initiatives that reduce the application attack surface.
Modern exposure management requires organizations to transition from reactive vulnerability chasing toward strategic risk reduction grounded in comprehensive visibility and predictive intelligence. The dashboard enables Risk Managers to see everything across the endpoint application landscape, exposing deployment patterns, version sprawl, and coverage gaps that create unnecessary security exposure. Machine learning-enhanced prioritization helps Security Operations Teams predict what matters by identifying vulnerabilities with genuine exploitation probability rather than theoretical risk divorced from threat actor behavior and organizational context. Armed with deployment prevalence and business impact context, teams act with confidence by mobilizing remediation resources toward exposures that represent actual threats to operations, compliance, and reputation. This unified vision brings enterprise views of application risk together as one coherent picture, while unified insight connects inventory patterns with vulnerability context to identify true exposures threatening business value, and unified action mobilizes Risk Managers, Security Operations Teams, and application owners to collaborate as one coordinated force addressing the exposures attackers would most likely weaponize against the Organization.
Components
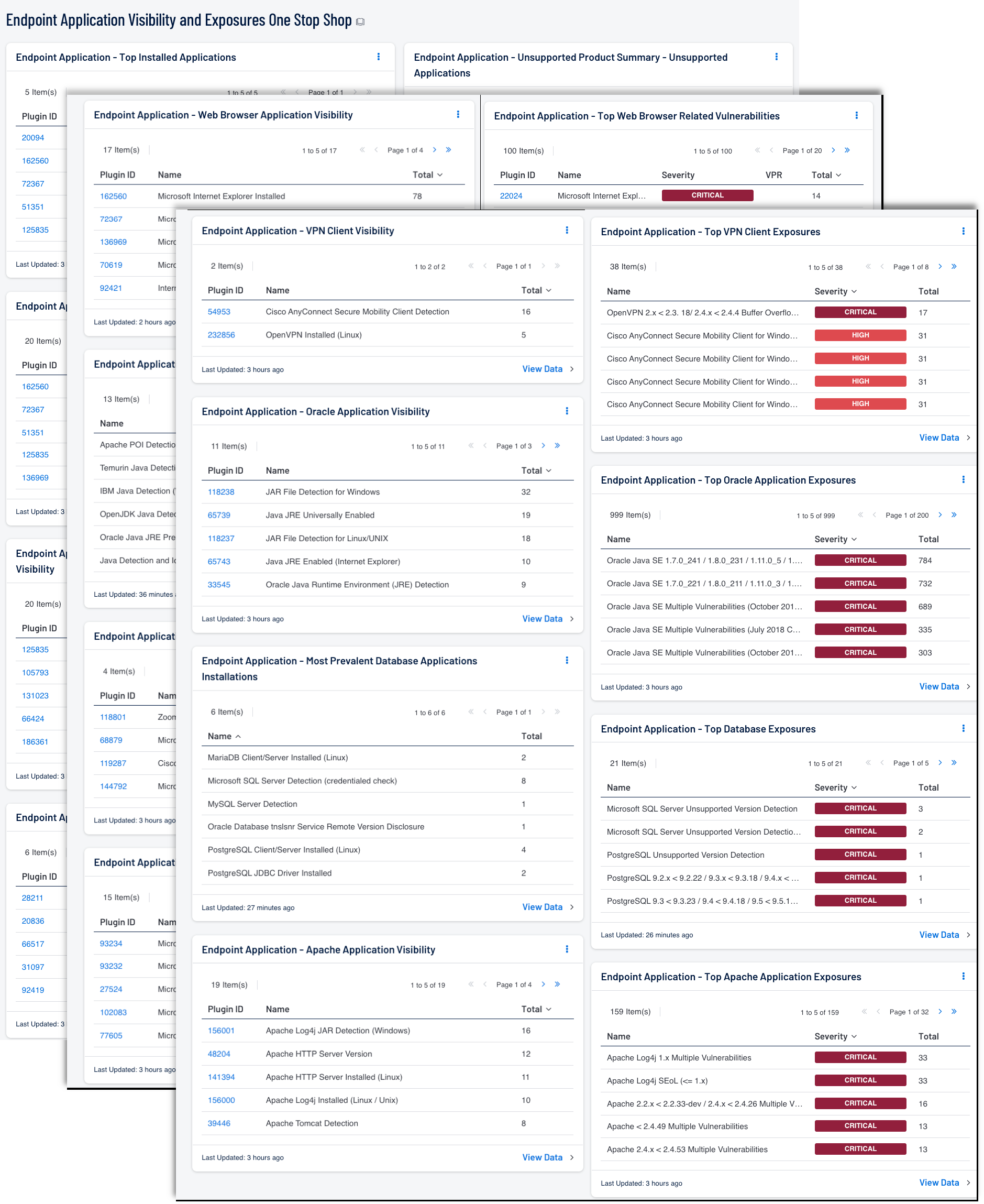
- Endpoint Application - Top Installed Applications: Risk Managers utilize this application inventory to identify the most widely deployed software across the infrastructure. The Organization gains insight into asset distribution patterns to support strategic decisions around licensing and security controls.
- Unsupported Product Summary - Unsupported Applications: This table displays all unsupported applications by name, sorted by count. Displayed is the plugin name, severity, and the total found. Unsupported software is any application, or operating system that is no longer maintained by the vendor. Unsupported software will typically no longer receive any updates, and will lack support. Organizations with unsupported software may be exposing themselves to security, operational, and compliance risks.
- Endpoint Application - Microsoft Application Installation Visibility: Risk Managers maintain awareness of productivity and enterprise software distribution patterns through this focused inventory. The Organization evaluates software standardization efforts by examining the variety and prevalence of deployed applications.
- Endpoint Application - Top Microsoft Application Related Vulnerabilities: Security Operations Teams prioritize remediation activities based on the most frequently occurring vulnerabilities affecting productivity software. Risk Managers allocate resources to address the exposures with the broadest impact across the enterprise application landscape.
- Endpoint Application - Installed Endpoint Management Application Visibility: The Organization maintains comprehensive awareness of management and security tooling deployed across endpoints and servers. Risk Managers verify coverage of critical monitoring and protection capabilities through this consolidated inventory.
- Endpoint Application - Top Endpoint Management Application Vulnerabilities: The Organization depends on endpoint management platforms to maintain security posture and operational oversight across distributed assets. Coordinated patching of management tooling requires careful planning to maintain continuous operational visibility throughout the update process.
- Endpoint Application - Adobe Application Visibility: Risk Managers track document viewing and creative content applications deployed across the infrastructure. The Organization evaluates the distribution of document reader and multimedia tools to inform standardization and security baseline requirements.
Endpoint Application - Top Adobe Application Exposures: Security Operations Teams address vulnerabilities in document viewing and multimedia applications that frequently serve as attack vectors. Risk Managers prioritize document reader vulnerabilities due to the ubiquity of document exchange in business workflows. - Endpoint Application - Web Browser Application Visibility: Security Operations Teams identify the web browsing capabilities deployed across the infrastructure to assess attack surface exposure. Risk Managers evaluate browser distribution patterns to inform security policy decisions and standard baseline requirements.
- Endpoint Application - Top Web Browser Related Vulnerabilities: Risk Managers prioritize browser vulnerabilities that affect the largest number of endpoints to reduce exposure to web-based attacks. Security Operations Teams coordinate rapid patching of browsing applications to close attack vectors commonly exploited in phishing and drive-by download campaigns.
- Endpoint Application - Java Installation Visibility: This table provides visibility into where Java applications are installed across your environment that you have scanned with Tenable.
- Endpoint Application - Top Java Exposures Sorted by Tenable VPR: This table reports on all Java vulnerabilities uncovered across the environment.
- Endpoint Application - Collaboration Application Visibility: Risk Managers maintain visibility into communication and conferencing tools that enable remote collaboration across the Organization. Security Operations Teams evaluate the deployment distribution of collaboration platforms to assess potential data exfiltration vectors.
- Endpoint Application - Top Collaboration Application Exposures: Security Operations Teams address vulnerabilities in collaboration platforms that handle sensitive business communications and file sharing. Risk Managers prioritize remediation of collaboration tool vulnerabilities due to the sensitive data these applications process.
- Endpoint Application - Office Application Visibility: The Organization tracks the deployment of document creation and presentation tools essential for business operations. Risk Managers assess office suite distribution to inform licensing decisions and version standardization initiatives.
- Endpoint Application - Top Office Application Exposures: Risk Managers prioritize office suite vulnerabilities that commonly serve as initial access vectors through malicious document campaigns. Security Operations Teams coordinate patching of productivity applications to reduce exposure to macro-based and document-embedded exploits.
- Endpoint Application - VPN Client Visibility: Security Operations Teams maintain awareness of remote access client distribution to ensure secure connectivity for remote workforce. Risk Managers evaluate VPN client deployment patterns to verify coverage of remote access security controls.
- Endpoint Application - Top VPN Client Exposures: Risk Managers prioritize remote access client vulnerabilities that could compromise the security boundary between remote users and corporate resources. Security Operations Teams coordinate urgent patching of remote access tools given the direct network access these applications provide.
- Endpoint Application - Oracle Application Visibility: The Organization tracks enterprise application and middleware components from a major enterprise software vendor. Risk Managers assess the distribution of database clients and application server components to inform infrastructure standardization decisions.
- Endpoint Application - Top Oracle Application Exposures: Risk Managers prioritize vulnerabilities in enterprise software components that support mission-critical business applications. Security Operations Teams coordinate patching activities for enterprise software while managing operational dependencies and application availability requirements.
- Endpoint Application - Apache Application Visibility: Security Operations Teams track open-source software components and web infrastructure applications deployed across the Organization. Risk Managers evaluate the distribution of open-source applications to assess support capabilities and update management processes.
- Endpoint Application - Top Apache Application Exposures: Risk Managers address vulnerabilities in open-source components that require the Organization to assume responsibility for security monitoring. Security Operations Teams coordinate patching of open-source software while tracking community-provided security updates and advisories.
- Most Prevalent Database Applications Installations: The following table displays the most prevalent Database applications across your environment enabling the user to have a quick glance at detected databases and their counts.
- Endpoint Application - Top Database Exposures: Risk Managers prioritize database vulnerabilities with urgency given the sensitive information these platforms store and manage. Security Operations Teams coordinate database patching activities while managing the complex dependencies between database updates and dependent application functionality.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success