CVE-2020-25213: Critical Vulnerability in File Manager WordPress Plugin Exploited in the Wild

Attackers have begun to target a vulnerability in a popular WordPress plugin with over 700,000 active installations, attempting to inject malicious code.
Update September 10, 2020: Updated the Title and Analysis sections of the blog to include the CVE identifier for this vulnerability, which was published to NVD on September 9.
Background
On September 1, researchers at Wordfence published a blog post about a critical vulnerability in File Manager, a popular WordPress Plugin used to manage files on WordPress sites. According to statistics from wordpress.org, the plugin is installed on over 700,000 active WordPress websites. In fact, on August 31, the plugin was downloaded nearly 84,000 times, the highest total daily downloads in all of 2020.
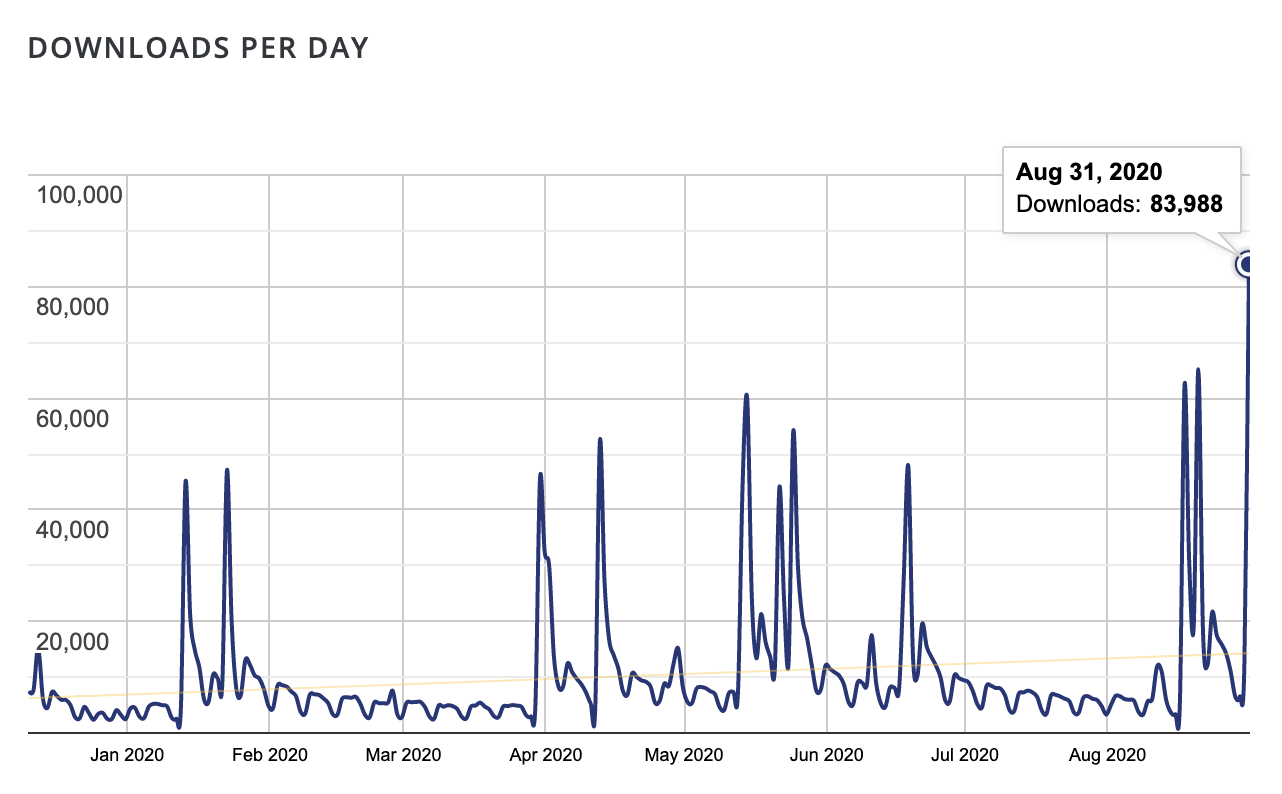
List of daily downloads for the File Manager plugin, which peaked at nearly 84,000 on August 31
Analysis
CVE-2020-25213 is a remote code execution flaw in the File Manager plugin for WordPress. It was assigned a CVSSv3 score of 10.0, the maximum CVSS score. According to Wordfence researchers, the flaw exists due to the improper inclusion of an open-source file manager library called elFinder. It appears that the file connector.minimal.php-dist was stored in an executable format (renamed to .php) and the file “could be accessed by anyone” in order to execute commands via a function in elFinderConnector.class.php.
An attacker could exploit this flaw by sending a specially crafted request to the connector.minimal.php file. Successful exploitation of this vulnerability would allow an attacker to gain remote code execution on the vulnerable WordPress site.
Wordfence notes they’ve observed attacks in the wild, blocking over 450,000 attempts to exploit this vulnerability. A full list of the indicators of compromise can be found in their blog post, and they include a list of files to monitor for in the /wp-content/plugins/wp-file-manager/lib/files path.
Proof of concept
A proof of concept (PoC) exploit script was published to a Github repository on August 25 from a security researcher with the pseudonym of w4fz5uck5. The PoC referenced two previous exploit scripts for CVE-2019-9194, a similar command injection vulnerability in the PHP connector of elFinder before version 2.1.48.
Solution
The File Manager plugin was updated to version 6.9 on September 1 to address this vulnerability by removing several elFinder library files from the plugin. WordPress users that use the File Manager plugin should upgrade to the latest version as soon as possible.
At the time this blog post was published, at least 71.5% of all active File Manager plugin installations are vulnerable, with version 6.5 accounting for over 26% of active installations. The wordpress.org plugin page marks 28.5% of active installations as “other” so it is possible that the actual number of vulnerable sites out there is quite larger.
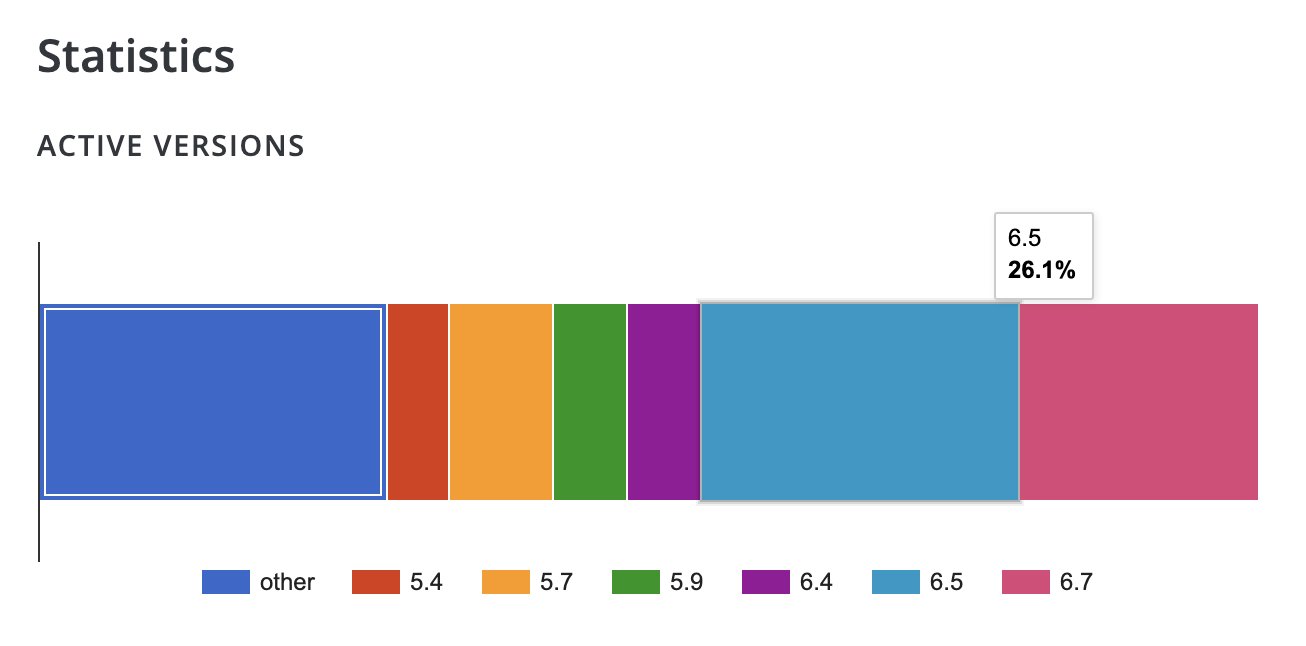
Active version statistics from the File Manager WordPress plugin page
Identifying affected systems
A list of Tenable plugins to identify this vulnerability will appear here as they’re released.
Get more information
- Wordfence Blog Post for File Manager Plugin Vulnerability
- File Manager Plugin Page on WordPress.org
- Changelog for File Manager Plugin to Address Vulnerability
- File Manager Vulnerability Proof of Concept Script
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.
Learn more
- Vulnerability Management




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success